In the modern digital landscape, APIs (Application Programming Interfaces) are essential for the functioning of applications They connect different parts of software—like the front end to the back end, or mobile apps to cloud services. They even help different companies communicate with each other. But because APIs are so widely used and often exposed, they have become a popular target for attackers—especially when they aren’t properly secured.
In this blog post, we’ll look at how ethical hackers, bug bounty hunters, and security researchers do API reconnaissance (recon) to discover APIs and find ways they might be abused. We’ll also explore three effective tools that assist in this process:
Nuclei
Postman
OWASP Amass
We’ll break down each phase: reconnaissance, enumeration, and vulnerability scanning—explaining them in simple language with practical context.
What Is API Recon?
API Reconnaissance (Recon) is the process of finding and analyzing the APIs that an application makes available. The main goal is to understand the attack surface—which means identifying the different API endpoints, the types of requests they accept, how they handle authentication, and whether they deal with any sensitive data.
In both security testing and bug bounty programs, recon is usually the first and most critical step. It helps answer key questions like:
Are security features like authentication or rate limiting missing?
What API endpoints are publicly accessible?
Are there any hidden or undocumented APIs?
Is the application leaking sensitive data through APIs?
OWASP Amass for API Recon
What is Amass?
OWASP Amass is a robust tool designed for both passive and active reconnaissance, with a strong focus on domain and subdomain discovery. It’s commonly used to uncover all the domains and subdomains that belong to a particular organization, helping security professionals map out the external attack surface.
Why use Amass for API Recon?
Many APIs are deployed on subdomains, like:
api.example.commobile-api.example.comdev-api.example.comstaging-api.example.com
Discovering these subdomains helps identify exposed APIs in development or staging environments, which might not have the same security standards as production.
Postman
What is Postman?
Postman is a widely-used tool for designing, testing, and interacting with APIs. Although it’s mainly used by developers, ethical hackers and security testers also rely on it to:
- Interact with and explore available API endpoints
- Send and repeat custom API requests
- Edit request headers, parameters, and body data
- Run basic security tests like fuzzing and injection attempts
How to perform API testing using Postman
- Import API Collections – If the API uses Swagger or OpenAPI specs, you can easily bring that into Postman. This lets you quickly view and test all available endpoints.
- Test Authentication – Try calling endpoints without logging in or providing tokens. If the API still responds with data, that’s a serious security issue.
- Test Rate Limiting – Use Postman’s Collection Runner to send many requests in a short time. If the API doesn’t block or slow down the traffic (e.g., with rate limits or CAPTCHA), it may be vulnerable to brute-force or abuse.
- Try Parameter Manipulation – Change values like user IDs, roles, or permissions in the URL or request body. If this gives you access to other users’ data, it could be an IDOR (Insecure Direct Object Reference) vulnerability.
Example:
Okay, let’s do the IDOR scenario step-by-step in crAPI.
Prerequisites:
- Make sure crAPI is running and you can access the web interface at
http://localhost:8888. - Postman has been installed on your system.
Attempt IDOR:
Log in to crAPI:
Open your web browser and go to http://localhost:8888.
Create a user account and log in.
Find the User Profile/Details Endpoint:
Once logged in, navigate to your profile page or any area where your user details are displayed.
Open the Developer Tools in your browser
Go to the “Network” tab.
As you navigate to your profile, look for an API request that fetches your user information. It might look something like /api/users/{your_user_id} or /api/profile. Select the request to examine its details, such as the URL, headers, and response.
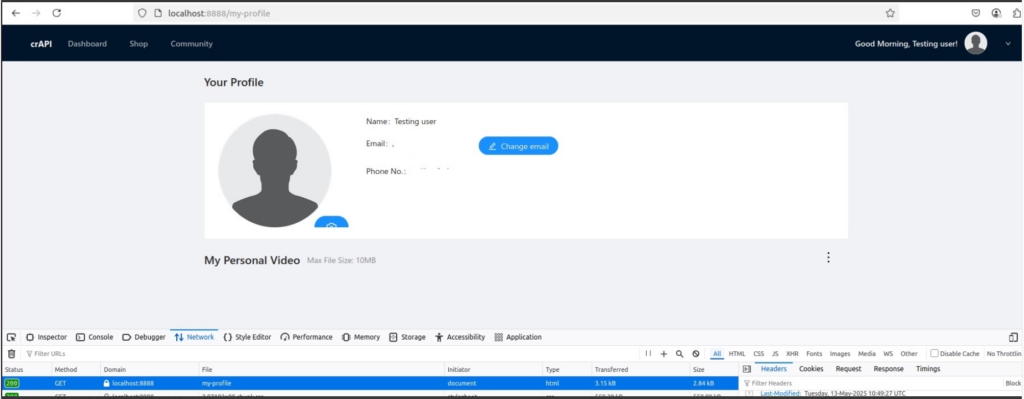
Let’s assume for this exercise that the endpoint to fetch user details is: http://localhost:8888/api/users/me or potentially something with a specific user ID like: http://localhost:8888/api/users/your user id.
Get Your User ID:
From the network request you identified in the previous step, note down your user_id.
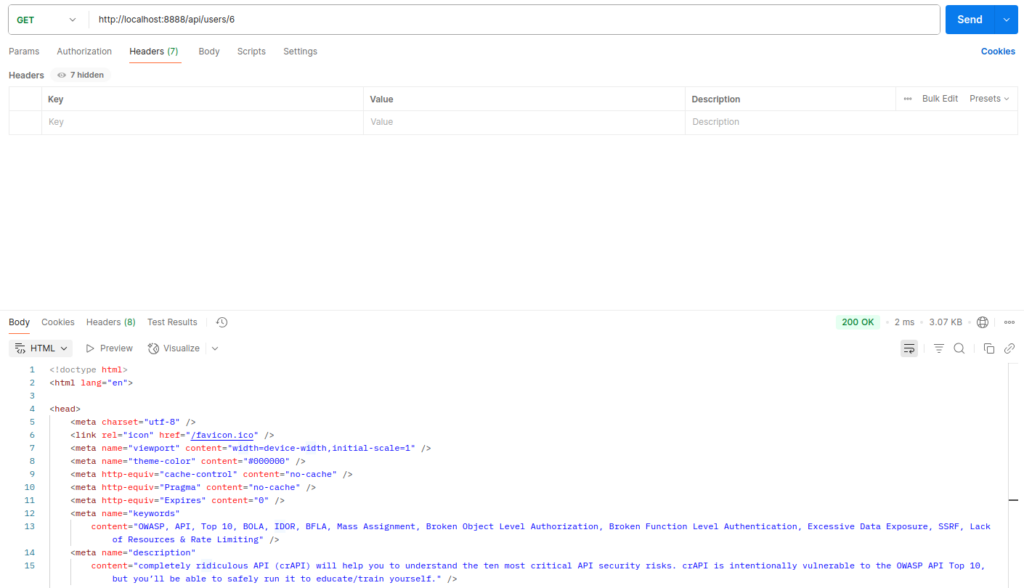
Test IDOR in Postman:
Open Postman.
Create a new GET request.
Type in the URL to get user details, making sure to substitute your user ID with the actual one.
http://localhost:8888/api/users/
Send this request. The response should contain your user information.
Nuclei for API Recon
What is Nuclei?
Nuclei is a fast and customizable vulnerability scanner that uses YAML-based templates to identify misconfigurations, CVEs, and exposures across APIs, web apps, and infrastructure.
How it helps in API abuse detection
Nuclei is a fast and flexible tool that comes with a large collection of community-created templates. These templates help detect issues such as:
- Weak or broken login systems
- Missing or unsafe HTTP headers
- APIs set up incorrectly
- Exposed debug or testing endpoints
- Leaked tokens or secrets in API responses
Nuclei is highly scriptable and designed for speed, making it perfect for automated scanning of API endpoints—especially those identified through tools like Amass or Postman.
Real-World API Abuse Examples
Here are some typical examples of API abuse in real-world scenarios such as.
BOLA (Broken Object Level Authorization) – An attacker modifies a user ID or object reference in an API request to gain access to another user’s data or actions they shouldn’t be allowed to perform.
Exposure of Sensitive Information – APIs sometimes return too much data in their responses, such as access tokens, credit card numbers, or detailed error messages that can help attackers.
Lack of Rate Limiting – When APIs don’t restrict the number of requests, attackers can perform actions like brute-force login attempts without being detected or blocked.
Exposed Development or Staging APIs – Test or development APIs are often left open without authentication but revealing internal application logic, secrets, or configurations that should be hidden.
Conclusion
API security is no longer optional. As more systems become interconnected through APIs and attackers will continue to exploit weaknesses in them. Fortunately, tools like OWASP Amass, Postman, and Nuclei make it easier than ever for defenders and testers to discover, test, and secure these critical interfaces.
Whether you’re an ethical hacker looking for your next bounty or a developer building the next great SaaS, mastering API recon and abuse techniques is an essential skill.
References
https://osintteam.blog/the-owasp-methodology-for-api-penetration-testing-c5c33ff8d2ca