Introduction
DevSecOps, or Secure DevOps, enhances the traditional DevOps practices by embedding security at every stage of the DevOps lifecycle. This integrated approach offers significant benefits, such as increased application and system security, enhanced security awareness among development and operations teams, automated security processes in the software development lifecycle, and reduced remediation costs by identifying security issues early in the development stages.
When applied to Azure Kubernetes Service (AKS), DevSecOps addresses the unique security considerations of different organizational roles, including developers, cloud engineers, and operations teams. This blog explores how DevSecOps can be effectively leveraged on AKS, detailing the lifecycle stages, best practices, and tools involved.
Key Benefits of DevSecOps
- Enhanced Security: Provides visibility into security threats and prevents vulnerabilities from reaching deployed environments.
- Increased Security Awareness: Fosters a culture of security awareness among development and operation teams.
- Automated Security Processes: Integrates security checks and processes into the CI/CD pipelines.
- Cost Reduction: Identifies and addresses security issues early, reducing the cost and effort required for remediation.
DevSecOps Lifecycle Stages on AKS
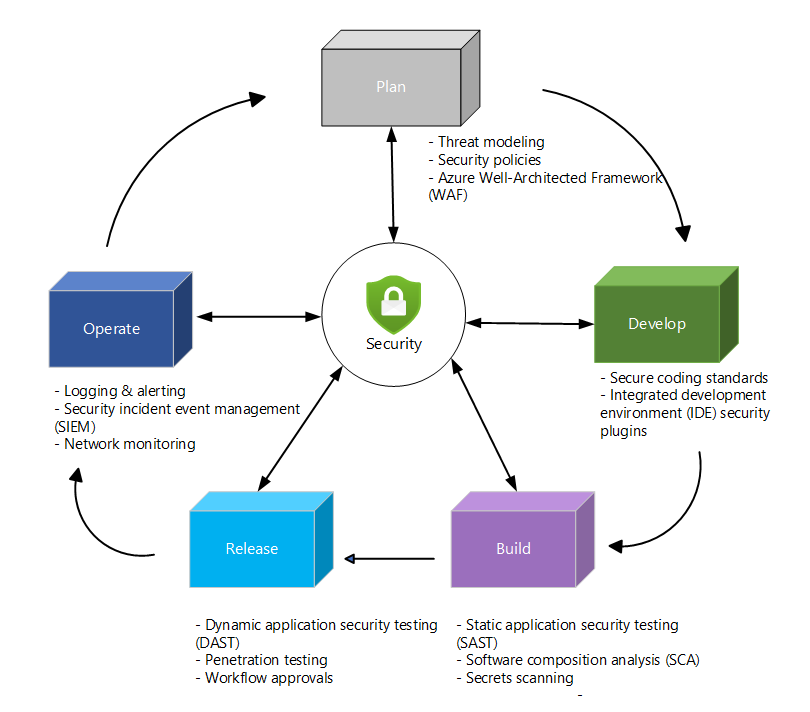
Plan Phase
The plan phase involves collaboration between security, development, and operations teams to ensure security is incorporated from the start.
Best Practices:
- Design a Secure Application Platform: Implement internal and external security components such as network firewalls and container registries.
- Threat Modeling: Use the STRIDE methodology to identify and mitigate threats early in the development process.
- Azure Well-Architected Framework (WAF): Apply WAF security and operational best practices for cloud-native environments.
Develop Phase
The develop phase emphasizes “shifting left,” integrating security early in the development lifecycle through secure coding practices and automated security checks.
Best Practices:
- Secure Coding Standards: Adopt OWASP secure coding recommendations and language-specific security practices.
- IDE Tools and Plugins: Use tools like SonarLint, Synk, and SARIF plugins to automate security checks within the development environment.
- Source Code Repository Controls: Implement branching methodologies, merge policies, and pre-commit hooks to ensure code security.
- Secure Container Images: Use minimal OS footprints, trusted base images, and tools like Trivy for vulnerability analysis.
Build Phase
During the build phase, automated security scans are integrated into CI pipelines to detect vulnerabilities in application source code and container images.
Best Practices:
- Static Code Analysis (SAST): Use tools like GitHub Advanced Security and kube-score to analyze code and Kubernetes objects for vulnerabilities.
- Secret Scanning: Enable secret scanning in GitHub and Azure DevOps to prevent the exposure of sensitive information.
- Software Composition Analysis (SCA): Use Dependabot and dependency review tools to monitor and manage open-source dependencies.
- Infrastructure as Code (IaC) Scans: Use Microsoft Defender for DevOps to scan IaC templates for misconfigurations.
- Secure Container Registries: Scan container images in Azure Container Registry for vulnerabilities and use digital signatures for image integrity verification.
Deploy Phase
The deploy phase focuses on establishing secure and controlled deployment pipelines for automated and secure code deployment to production environments.
Best Practices:
- Access and Workflow Control: Use branch protection rules, environments, and approval gates to manage deployment pipeline access.
- Secure Deployment Credentials: Leverage OpenID Connect for secure resource access and adopt GitOps for reduced security risks.
- Dynamic Application Security Testing (DAST): Run DAST tests using GitHub Actions and tools like ZAP for web application security.
- Trusted Registries: Enforce deployment from trusted registries using Azure Policy and Defender for Containers.
Operate Phase
In the operate phase, continuous monitoring and security monitoring ensure the production environment remains secure and compliant.
Best Practices:
- Microsoft Defender for Cloud: Implement automated scanning, configuration monitoring, and vulnerability assessments.
- Kubernetes Cluster Updates: Regularly update AKS clusters using AKS platform tools and maintenance features.
- Azure Policy for Governance: Apply Azure Policy for security and governance of AKS clusters, and use network policies for secure traffic management.
- Azure Monitor for Continuous Monitoring: Use Azure Monitor for log and metric collection, continuous monitoring, and alerting on suspicious activity.
- Microsoft Sentinel for Threat Monitoring: Integrate AKS logs with Microsoft Sentinel for centralized security monitoring and real-time threat detection.
- Audit Logging: Enable audit logging to monitor cluster activity and integrate logs with SIEM solutions like Microsoft Sentinel.
Conclusion
Implementing DevSecOps on Azure Kubernetes Service (AKS) involves embedding security practices and tools across all stages of the DevOps lifecycle. By adopting best practices such as secure coding standards, automated security scans, and continuous monitoring, organizations can significantly enhance their security posture, reduce remediation costs, and ensure compliance with enterprise security standards. This comprehensive approach to security helps create robust, secure applications and infrastructure in a cloud-native environment.


