Understanding the Need for IoT Security Testing
The Internet of Things (IoT) has revolutionized the way we interact with technology, connecting everything from smart homes to industrial machinery. However, this vast interconnected network opens doors to potential cyber threats. Penetration testing, or ethical hacking, helps address these vulnerabilities by simulating real-world attacks to identify and mitigate risks .
Why Penetration Testing for IoT Devices Is Crucial
IoT devices are often overlooked in traditional security protocols. However, they hold critical importance:
- Exposure to Sensitive Data: IoT devices gather operational and personal data.
- Operational Risks: A compromised device can disrupt vital systems.
- Gateway for Cyberattacks: Weak devices can serve as entry points for broader network breaches.
Common Security Challenges in IoT Devices
While IoT has grown, security has lagged behind. Typical vulnerabilities include:
- Weak Authentication: Default or weak passwords are a common flaw.
- Communications Without Encryption: Information sent without encryption is vulnerable.
- Lack of Updates: Devices often run outdated firmware with unresolved security issues.
- Overlooked Design Flaws: Security is often not a priority during product development.
How Penetration Testing Secures IoT Devices
Penetration testing examines all potential attack surfaces, ensuring devices are resilient against threats. The process involves:
- Discovering Weak Points: Identifying gaps in device security.
- Exploiting Vulnerabilities: Testing the extent and impact of flaws.
- Providing Fixes: Offering actionable steps to secure devices and networks.
Essential Phases of IoT Penetration Testing
- Reconnaissance: Collect device-specific data such as protocols, services, and firmware details.
- Vulnerability Scanning: Identify known security issues using tools like Nessus or OpenVAS.
- Exploitation: Attempt controlled attacks to test the exploitability of vulnerabilities.
- Reporting and Remediation: Deliver detailed reports and suggest security improvements.
Tools for Effective IoT Penetration Testing
Shodan: For discovering connected IoT devices online. (https://www.shodan.io/)
Binwalk: To analyze firmware and detect vulnerabilities. (https://github.com/ReFirmLabs/binwalk)
Burp Suite: Helpful for testing APIs and web interfaces for the Internet of Things. (https://portswigger.net/burp)
Kali Linux: A powerful penetration testing toolkit. (https://www.kali.org/)
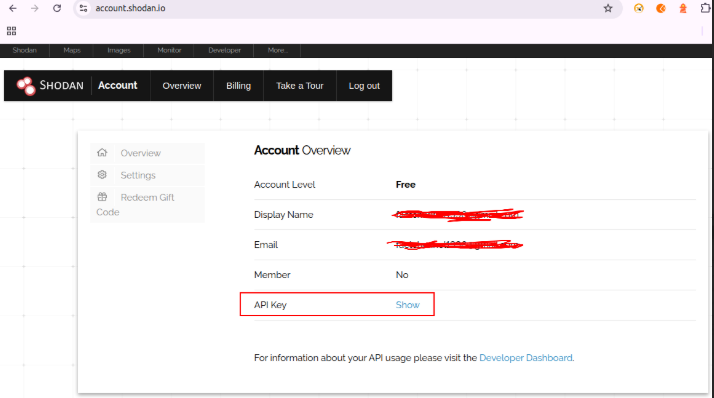
Shodan Case Study
A search engine for internet-connected devices, allowing you to discover and map devices on the network, identify open ports, and gather information about their software and hardware.
Steps:
- Obtain Shodan API Key: Sign up for a free Shodan account at https://www.shodan.io/ to obtain an API key.
- Construct Search Query: Define your search criteria using Shodan’s query language. In this example, the query
"telnet"searches for devices with Telnet service running. - Build API URL: Construct the API URL using the Shodan API endpoint (
https://api.shodan.io/shodan/host/search) and your API key. - Send API Request: Use Python’s
requestslibrary to send a GET request to the constructed URL. - Process Response:
- Check for successful response status code (200).
- If successful, parse the JSON response to extract details about the discovered devices.
- Print the total number of devices found.
- Loop through each device and print its IP address and hostname (if available).
- Handle Errors: Print an error message if the API request fails.
Python Code:
import requests
# Replace with your free Shodan API key
API_KEY = "YOUR_SHODAN_API_KEY"
# Search query (replace with your desired criteria)
search_query = "telnet"
# Build the API URL
url = f"https://api.shodan.io/shodan/host/search?key={API_KEY}&q={search_query}"
try:
# Send GET request using requests library
response = requests.get(url)
response.raise_for_status() # Raise an exception for non-200 status codes
# Process successful response
data = response.json()
total_results = data.get('total', 0)
print(f"Found {total_results} devices with Telnet service (free tier might limit results).")
for device in data.get('matches', []):
ip_address = device.get('ip_str', 'Unknown')
hostname = device.get('hostnames', [])[0] if device.get('hostnames', []) else 'Unknown'
print(f"IP: {ip_address}, Hostname: {hostname}")
except requests.exceptions.RequestException as e:
print(f"Error: {e}")
except Exception as e: # Handle other potential exceptions
print(f"Unexpected error: {e}")Terminal Response:-
Found 5 devices with Telnet service
IP: 203.0.113.1, Hostname: Unknown
IP: 104.198.151.238, Hostname: Unknown
IP: 172.217.160.121, Hostname: Unknown
IP: 192.168.1.100, Hostname: my-home-server
IP: 8.8.8.8, Hostname: dns.google Remember:
- Replace
"YOUR_SHODAN_API_KEY"with your actual Shodan API key. - This is a basic example. Shodan offers a powerful query language for more complex searches.
- Always use Shodan responsibly and ethically.
Implementing Security Post-Testing
After testing, strengthening security involves:
- Frequent Updates: Use the most recent fixes to keep firmware current.
- Authentication Practices: Use strong passwords and implement two-factor authentication.
- Data Protection: Encrypt all data to secure it during transmission and storage.
- Network Isolation: Segment IoT devices from critical systems.
Overcoming Challenges in IoT Penetration Testing
Testing IoT devices presents unique hurdles:
- Diversity of Devices: Each device may require tailored testing.
- Limited Resources: Constrained memory and CPU power on IoT devices can limit tools.
- Legal Considerations: Testing must respect intellectual property and privacy laws.
Conclusion
Penetration testing is a critical step in securing IoT ecosystems. As IoT continues to expand, organizations and manufacturers must prioritize robust security measures to protect sensitive data and maintain operational integrity. We can take advantage of IoT without sacrificing security by proactively fixing vulnerabilities.


