In today’s Microservices-driven architecture, security is not just about verifying user identity or checking if a user can access a certain service or not. As we know System has more distributed and it handles sensitive business operations, there is a growing need to perform a fine grain access control. With the help of this users can perform only the specific actions which they can access it.
In this blog, we’ll walk through how to implement Fine-grained access control in microservices using Spring Security and JWT claims. By leveraging JWT Claims and spring security, we can apply access rule at a detailed level within each microservice.
What is Fine-grained access control?
Fine-grained access control is a security method that controls who can access specific data. It allows that we can control over specific fields in a response and we can perform particular actions on a resource.
Unlike coarse-grained access control, it typically grants broad permissions like that Admin can access all the endpoints. But Fine-grained Access Control, it grants only the user specific permissions. It also ensures more precise, secure and context aware access management.
Consider a Real-world use case: In an enterprise HR management system, employees, managers, and HR admins have different access levels. With the help of Fine-Grained access control Employees can edit their profiles, managers can view direct reports, and HR admins can access all records of the employees.

How can we use Fine-Grained Access Control?
Here are some of the use cases of Fine-grained access control that we can use in microservices :
Use case 1: Multiple Data Sources Stored Together
In the cloud, we know large amount of data types store in one place. We cannot just provide whole access for these storage segments based on the roles; there are some data types that can be access by a particular role and others cannot accessed that data type. Fine-Grained access control is crucial because it provides the access to a particular role even when they are stored all together.
Use case 2: Different Levels of Access Based on User Roles
One of the most powerful benefits of fine-grained access control that it provides different levels of access as compared to the pass/fail structure based on their role to which they belong. In coarse-grained systems, information can merely exist as one of two types allowed or not allowed, it depends on the person who is trying to access it. But with fine-grained access control, there can be a little more nuance and variation.
Use case 3: Securing Mobile Access
Most of the companies are offering support for accessing data remotely using mobile devices, such as mobile phones. On the other hand, Individuals working from home or at varied times are stretching the standard workday. With this in mind, companies may need to implement data access control. That controls are not only role or identity based but also time or location based.
Fine grained access control makes this possible. You can restrict access permissions to a specific location. After this employee cannot access it from third party wireless servers that may be exposed to breaches.
Use case 4: Third party Access
In Most times, a company that works with other business (a B2B company) want to give a third-party access to some of its data stored in the cloud. But they don’t want to risk that data being changed or exposed to other companies. Fine-Grained access control helps by allowing the read only access to the company. So, the third party can see that data only, they cannot change it. This thing helps to keep everything safe and secure.
What are Jwt claims?
Jwt claims are pieces of information or self-contained tokens that carry information about the user and their permissions. They help manage authentication and authorization for applications and APIs by granting access according to the user’s role. JWT claims allow the server to identify the user, what things they can access and perform and check how long the token remains valid. In this below example, the following JSON object contains three claims (sub, name, admin):
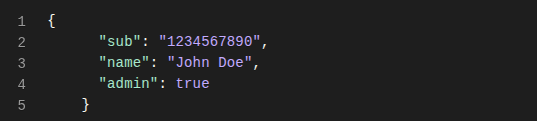
In this example, an Id token (which is always a JWT) can contain a claim called name. This claim states that the name of the user authenticating is “John Doe”.
Implementing Fine-Grained Access Control
1. hasAuthority Example:
@PreAuthorize("hasAuthority('view_orders')")
public List<Order> getOrders() {
return orderService.findAll();
}This getOrders method allows access only to users who have the view_orders authority. Spring Security checks the JWT or user context to ensure that the user has this authority or permission before executing any method.
2. Custom Method Access Check
@PreAuthorize("@accessChecker.canAccessRegion(authentication, 'north-america')")
public List<Employee> getEmployeesInRegion() {
return employeeService.findByRegion("north-america");
}Here, custom logic is applied through a method in accessChecker. This annotation checks whether the current user has access to a specific region. getEmployeesInRegion() method retrieves a list of employees in the north-america region.
3. Method with Multiple claims (Role + permission)
@PreAuthorize("hasRole('HR') and hasAuthority('edit_salary')")
public void updateSalary(SalaryUpdateRequest request) {
salaryService.update(request);
}This method updateSalary method allows access only to users with both the HR role and edit_salary permission in their JWT claim. In this @PreAuthorize annotation confirms that both conditions are met before executing any method. If the user lacks either the role or this permission, The system denies access.
Conclusion
In today’s distributed microservices architecture, simply verifying user roles is no longer sufficient. As we all know Software applications become more complex and has more data sensitive, Fine-grained access control using spring security and JWT claims is a must to ensure users can do only do the actions they are specially authorised to, Nothing more, nothing less.
Using Spring Security together with JWT Claims, Developers can apply more specific and context-based authorization across different services. This feature not only helps make the system more secure but also enables more flexible, scalable and secure access control based on roles, regions and time, and even custom business logic.
References
https://www.styra.com/blog/what-is-fine-grained-access-control/


