In the modern world of web applications, Single Sign-On (SSO) makes logging into modern apps convenient, but when misconfigured, it can open dangerous doors for attackers. This blog shows how pen testers and security researchers can identify and exploit flaws in OAuth-based authentication, particularly when Multi-Factor Authentication (MFA) is used.
We’ll simplify the jargon, use hands-on examples, and guide you through tools like OAuth2 Proxy, mitmproxy, Evilginx, and OauthTester.
What is OAuth 2.0 (in simple words)?
OAuth 2.0 is like giving a valet your car key, but only letting them park the car, not drive away. That token tells them, “This person can access the garage, but not the vault.”
Apps (like Facebook or Google) give access tokens to other apps (like Instagram or Zoom) so they can act on your behalf, without knowing your password..
- Authorisation Server: Like a hotel receptionist who gives out keycards.
- Access Token: Like a temporary keycard.
- Scopes: Define what the keycard (token) can open.
- Refresh Token: Lets you extend your stay without talking to the receptionist again.
🧭 What is SSO and MFA?
- Single Sign-On (SSO): Login once, access many apps. For example, using your Google account to access YouTube, Drive, and Gmail.
- Multi-Factor Authentication (MFA): MFA means logging in with something you know (password) and something you have (phone/code).
- But here’s the catch: OAuth tokens are issued after MFA, which means if an attacker steals the token, they bypass MFA completely.
Real-World Problem: When OAuth Gets Messy
OAuth flows can be misused to bypass MFA or access unauthorised resources if:
- Tokens are reused
- Redirects are not validated
- Scopes are too broad
- MFA is enforced only at login, not during token reuse
Real-World Misconfigurations and Exploits
1. Token Reuse and Session Fixation
Imagine a scenario where a user logs into a web application using OAuth. The authorisation server issues an authorisation code, which the application exchanges for an access token. If the application does not properly invalidate the authorisation code after use, an attacker could reuse it to obtain a new access token, gaining unauthorised access to the user’s data.
- Set up OAuth2 Proxy:
- Configure OAuth2 Proxy to authenticate users via an OAuth provider (e.g., Google).
- Ensure the proxy is correctly set up to handle OAuth tokens.
- Intercept OAuth Flow:
- Use a tool
mitmproxyto intercept the OAuth flow. - Capture the authorisation code issued by the OAuth provider.
- Use a tool
- Reuse Authorisation Code:
- Attempt to reuse the captured authorisation code to request a new access token.
- If the server does not invalidate the code after the first use, you will receive a new access token, demonstrating token reuse vulnerability.
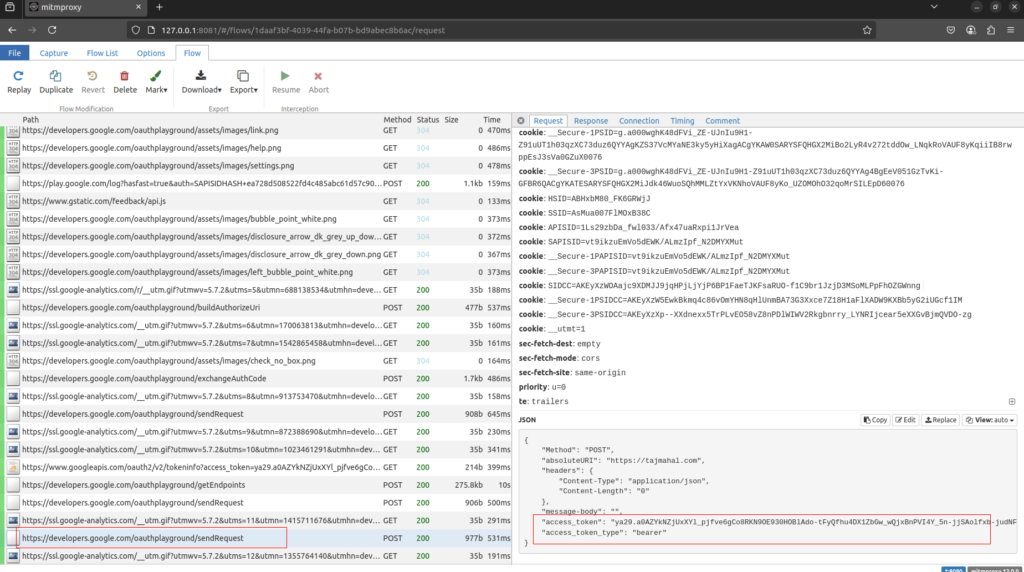
Mitigation: Ensure authorisation codes are single-use and immediately invalidated after being exchanged for an access token.
2. Open Redirect Vulnerabilities
Consider a web application that uses OAuth for authentication. If the application does not strictly validate the redirect URI, an attacker could manipulate it to redirect the user to a malicious site. For example, the attacker could craft a URL that redirects the user to https://malicious.com, where the OAuth token is captured.
- Set up mitmproxy:
- Install and configure
mitmproxyto intercept web traffic. - Set up your browser to use
mitmproxyas the proxy server.
- Install and configure
- Identify Redirect URI:
- Browse the target application and identify the OAuth redirect URI parameter.
- Use
mitmproxyto modify the redirect URI to a malicious site (e.g.,https://malicious.com).
- Capture Token:
- When the OAuth flow redirects to the modified URI, the access token will be sent to the malicious site.
- Capture the token and demonstrate how it can be used to gain unauthorised access.
Mitigation: Implement strict validation of redirect URIs, allowing only exact matches and avoiding wildcards
3. Improper Scope Enforcement
In another scenario, an application requests overly broad scopes during the OAuth authorisation process. For instance, an application might request access to a user’s email, contacts, and calendar when it only needs access to the email. This unnecessary access increases the risk of data exposure.
In short, by keeping the permissions limited to what is necessary, you can reduce the risk of unnecessary data exposure.
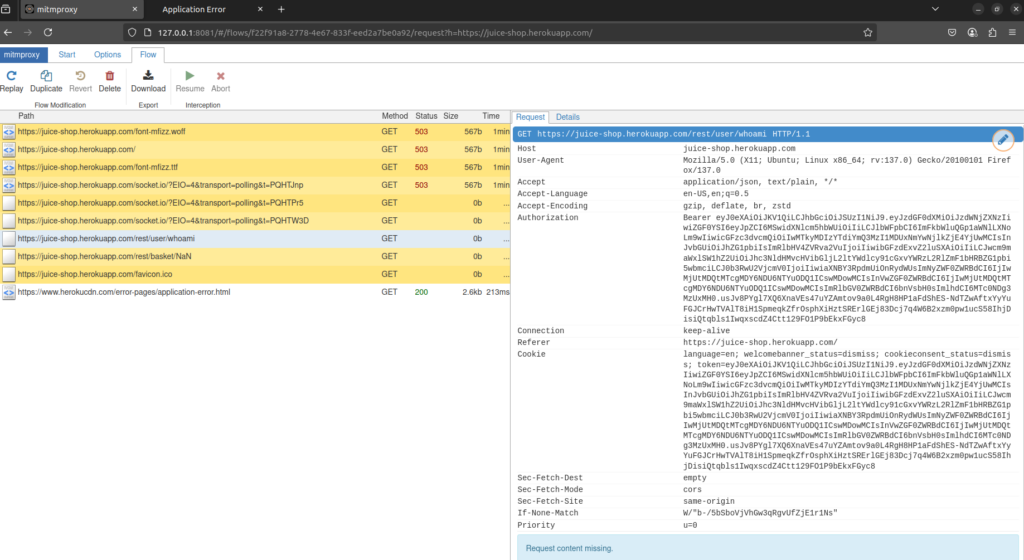
- Set up Evilginx:
- Install and configure
Evilginxto act as a man-in-the-middle proxy. - Create a phishing site that mimics the legitimate OAuth login page.
- Install and configure
- Phish for Credentials:
- Send a phishing link to the target user, directing them to the fake login page.
- Capture the user’s credentials and OAuth tokens as they log in.
- Access with Broad Scopes:
- Use the captured tokens to access the user’s data with the overly broad scopes requested during the OAuth authorisation process.
- Demonstrate how unnecessary access can lead to data exposure.
Mitigation: Request only the minimum necessary scope for the application’s functionality.
Preventing MFA Bypass with Proper Token Validation
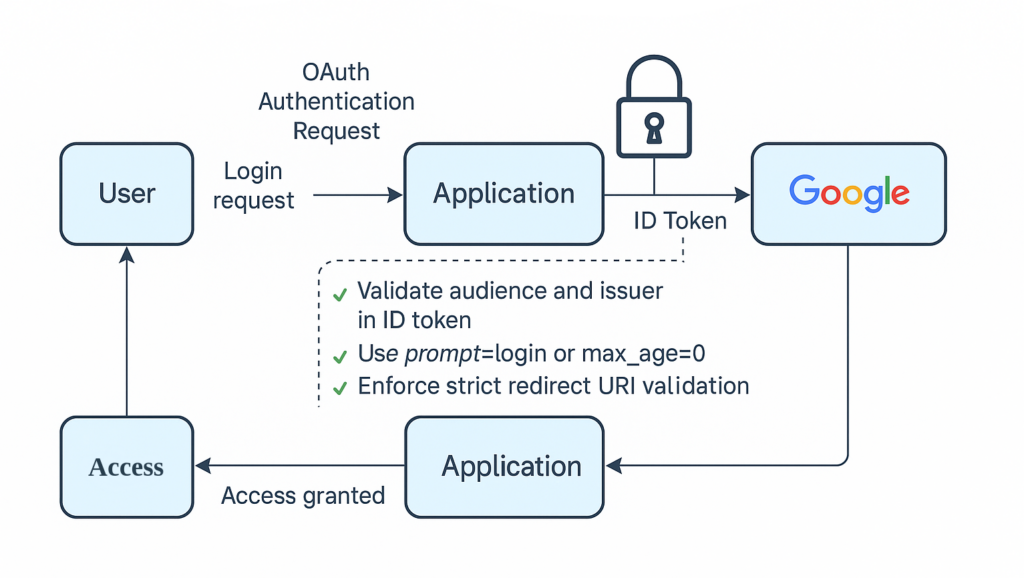
🔐 Best Practices to Prevent OAuth Abuse
| ✅ Do This | ❌ Don’t Do This |
|---|---|
| Use short-lived tokens | Issue long-lived access tokens |
| Implement token binding (IP/device) | Accept tokens without context |
| Rotate session cookies after login | Reuse pre-auth cookies |
| Validate redirect URIs strictly | Accept any subdomain or wildcard |
| Re-prompt MFA for sensitive scopes | Treat all scopes equally |
| Use PKCE with public clients | Skip PKCE in mobile/web apps |
Conclusion
OAuth enhances the flexibility of modern applications, but if not implemented correctly, it can also widen the attack surface. With the right tools and knowledge, penetration testers can uncover significant security issues, including the potential to bypass multi-factor authentication (MFA). It is crucial for developers to thoroughly test their workflows and adhere to best practices to avoid these vulnerabilities. Understanding and testing for common OAuth misconfigurations can greatly enhance the security of single sign-on (SSO) implementations in modern applications. Use tools like OAuth2 Proxy, mitmproxy, Evilginx, and OauthTester to identify and mitigate vulnerabilities that attackers could exploit to bypass MFA.
Security is not just about passwords and firewalls — it’s about understanding how protocols behave in the real world.
We’re just getting started by leveraging advanced security testing techniques! Stay tuned for more valuable insights in upcoming posts. For deeper dives into related topics, be sure to visit our blog regularly, Test Automation NashTech Blog.