In today’s digital landscape, cloud security in general—and AWS Cloud Security in particular—is critical to business operations. While cloud adoption offers numerous benefits, it also introduces various security challenges. This blog post will explore common AWS security concerns and Amazon’s comprehensive measures to address them. We’ll also highlight our expertise in identifying, mitigating, and monitoring threats to ensure your cloud environment remains secure and compliant.
Cloud Security Risks
A well-defined security framework is indispensable in the dynamic world of cloud computing. Categorizing cloud security ensures that organizations can focus their efforts and mitigate risks effectively. Cloud security can be categorized into broad areas based on organizations’ threats and challenges. Here’s a breakdown of some common categories.
1. Infrastructure Security
Infrastructure security forms the foundation of a secure cloud environment. It safeguards the hardware, software, and networks that underpin your cloud applications and data. By securing your infrastructure effectively, you protect sensitive information and guarantee the availability and reliability of your cloud services. Prioritizing strong infrastructure security measures helps mitigate risks, protect your organization’s reputation, and sustain business continuity. When focusing specifically on AWS cloud infrastructure security, there are three key components to consider:
- AWS Networking: Protecting the network infrastructure that connects cloud resources.
- Compute security: Securing virtual machines, containers, and serverless functions.
- Storage security: Protecting data stored in the cloud, including data at rest and in transit.
2. Data Security
AWS Data Security protects your data at every stage of its lifecycle, from storage to transmission. Leveraging advanced encryption, access controls, and continuous monitoring, AWS ensures your data remains secure, compliant, and resilient against threats. Using AWS’s robust data security services, you can safeguard sensitive information, maintain privacy, and meet regulatory requirements, letting you run confidently in the cloud.
- Data privacy: Ensuring compliance with data privacy regulations (e.g., GDPR, CCPA).
- Data classification: Categorizing data based on sensitivity and value to decide appropriate security measures.
- Data loss prevention (DLP): Preventing unauthorized access, use, or disclosure of sensitive data.
3. Application Security
AWS Application Security provides comprehensive protection for your cloud-based applications, ensuring they are secure, resilient, and compliant. AWS includes features like automated security assessments, identity and access management, and threat detection, which help safeguard your applications against vulnerabilities and attacks. By leveraging AWS’s application security services, you can build secure applications and deploy applications that preserve the integrity and confidentiality of your data.
- Web application security: Protecting web applications from vulnerabilities like SQL injection, cross-site scripting (XSS), and cross-site request forgery (CSRF).
- API security: Securing application programming interfaces (APIs) to prevent unauthorized access and data breaches.
- Runtime security: Protecting applications from attacks during execution.
4. Identity and Access Management (IAM)
Identity and Access Management (IAM) is critical to cloud security. It ensures that the right individuals have the appropriate access to your AWS resources. IAM helps protect your cloud environment from unauthorized access by managing permissions and authentication. This maintains the integrity and security of your data and applications.
- Identity management: Managing user identities and credentials.
- Access management: Controlling who can access what resources and under what conditions.
- Privileged access management (PAM): Managing access to privileged accounts with elevated permissions.
5. Threat Detection and Response
With robust Threat Detection and Response capabilities, AWS empowers you to find potential security threats. You can assess and respond to these threats in real-time. Advanced tools like Amazon GuardDuty, AWS Security Hub, and AWS Shield can be used. These tools help you detect anomalies, mitigate risks, and guarantee continuous protection of your cloud environment. This proactive approach to threat management helps you stay ahead of emerging threats. It ensures the safety and resilience of your applications and data.
- Security monitoring: Continuously monitoring cloud environments for suspicious activity.
- Threat detection: Identifying potential security threats and vulnerabilities.
- Incident response: Responding to security incidents effectively and efficiently.
6. Compliance
Compliance on AWS is designed to help you confidently meet regulatory and industry standards. AWS provides a comprehensive suite of compliance tools, including certifications and controls. These allow you to keep security and governance across your cloud environment. By leveraging AWS’s compliance services, you can ensure that your data, applications, and operations adhere to the highest standards. This reduces risk and builds trust with your stakeholders.
- Regulatory compliance: Ensuring adherence to industry-specific regulations (e.g., HIPAA, PCI DSS).
- Audit and certification: Conducting security audits and obtaining relevant certifications (e.g., ISO 27001, SOC 2).
- Governance and risk management: Establishing policies, procedures, and frameworks to manage security risks.
7. Cloud-Specific Security
Cloud-specific security on AWS is tailored to handle the unique challenges and risks of operating in the cloud. AWS offers a range of specialized security tools and services designed to protect cloud-native applications, secure data across distributed environments, and ensure compliance with dynamic cloud regulations. By implementing cloud-specific security measures, you can safeguard your resources, optimize security practices, and confidently manage your cloud infrastructure in a rapidly evolving digital landscape.
- Cloud service provider (CSP) security: Evaluating the security practices and certifications of the CSP.
- Hybrid cloud security: Securing environments that combine on-premises and cloud resources.
- Multi-cloud security: Managing security across multiple cloud platforms.
AWS Security – Shared Responsibility Model
The Shared Responsibility Model in cloud computing is a framework that delineates the security responsibilities between the cloud service provider, such as AWS, and the customer. This model ensures that while the cloud provider manages the security of the cloud, the customer is responsible for security in the cloud. By clearly defining these roles, the Shared Responsibility Model helps organizations understand their obligations and implement the security measures to protect their data and applications in the cloud environment.
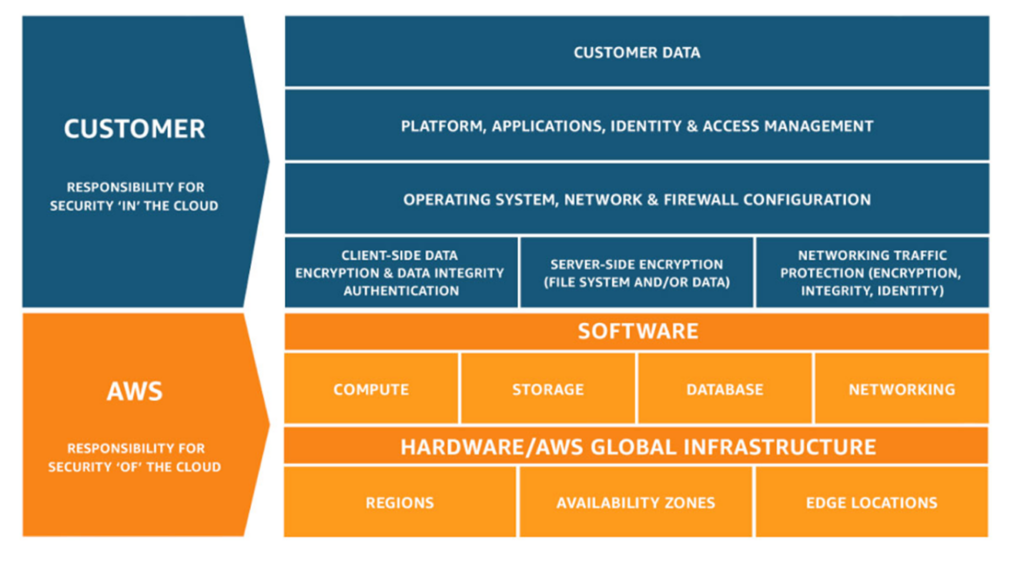
- Customer responsibility will be determined by the AWS Cloud services that a customer selects.
- AWS is responsible for protecting the infrastructure that runs all the services offered in the AWS Cloud.
Risk Level Likelihood Matrix for AWS Cloud Security
In any environment, whether industry-specific, regionally governed, or technologically driven, the ultimate goal of implementing controls is to manage and mitigate risk effectively. The Risk Level Likelihood Matrix is a powerful tool in this process, enabling us to evaluate and prioritize risks based on their likelihood and potential impact. By systematically assessing these factors, we can focus our efforts on the areas where risk poses the greatest threat, ensuring that our risk management strategies are targeted and efficient.
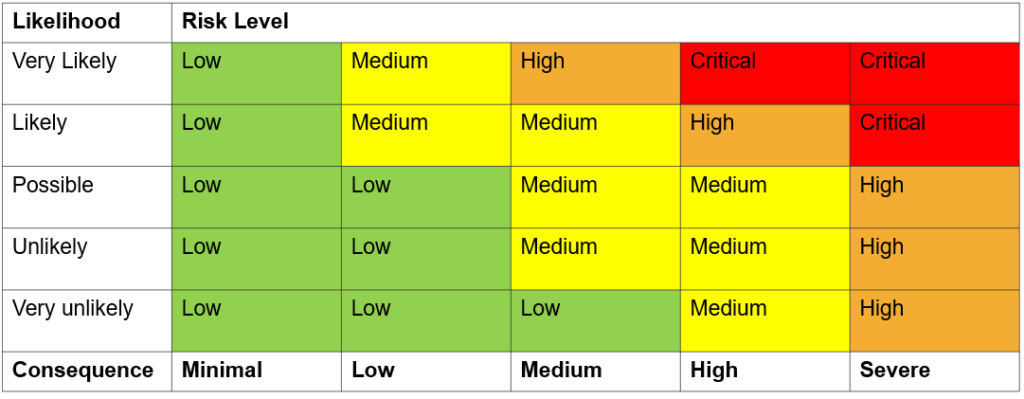
- The likelihood is based on the frequency of previous occurrences.
- The consequence is based on the financial, reputational, and time cost of the event.
Multi-layered Security Landscape
Our company implements a Multi-layered Security approach to effectively address cloud security risks. Each layer is designed to address multiple categories of cloud security concerns, working cohesively to provide comprehensive protection.
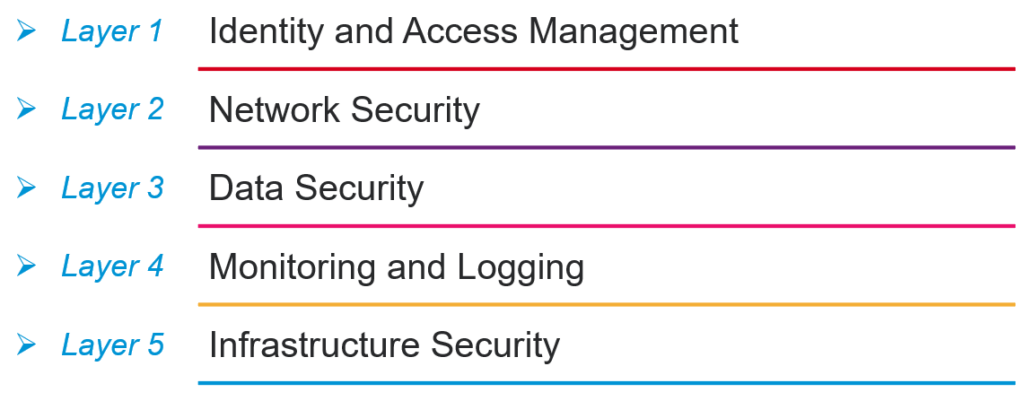
The concept of a Multi-layered Security Landscape refers to the strategic approach of protecting an organization’s assets by implementing multiple layers of security controls, each designed to address different aspects of potential threats. Rather than relying on a single line of defense, a multi-layered security approach creates a comprehensive shield that encompasses everything from the physical security of data centers to advanced cybersecurity measures like encryption, intrusion detection, and access controls.
By layering these defenses, organizations can mitigate risks more effectively, as each layer provides an additional opportunity to detect, prevent, or respond to security threats. This approach recognizes that no single control is foolproof and that a robust security posture requires overlapping protections to safeguard data, applications, and infrastructure against an ever-evolving landscape of threats.
- Layer 1: Identity and Access Management
- Layer 2: Network Security
- Layer 3: Data Security
- Layer 4: Monitoring and Logging
- Layer 5: Infrastructure Security
AWS Security Recommendations – Quick Recap
To ensure robust security in your AWS environment, it is essential to follow key recommendations: implement strong Identity and Access Management (IAM) controls, including the principle of least privilege and multi-factor authentication; encrypt data both at rest and in transit; continuously monitor and log activities using AWS services like CloudTrail and GuardDuty; regularly audit your configurations and automate security through Infrastructure as Code (IaC); and stay compliant with industry standards by leveraging AWS’s built-in compliance tools. These best practices help safeguard your cloud infrastructure against evolving threats while maintaining compliance and operational efficiency. When we implement Multi-layered Security, we will strictly follow these best practices. Please look; we can have a shared sense of these best practices.
1. Implement a Strong Identify Foundation
- Identifying identities that will access your resources
- Use a centralized identity provider
- Ensure proper authentication, enforce the use of MFA
- Remember the least privilege principle
2. Apply Security at All Layers
- Keep up-to-date diagrams of your assets and topologies.
- Implement trust boundaries, segmentation, configuration, policy enforcement points, etc.
- Clearly define and separate publicly facing services from internal services.
- Deploy your resources to a secured network and use access control policies.
3. Prepare for Security Events
- Consider all the bad things that can happen and how you will respond.
- All those actions should be put into a Response Plan.
4. Enable Traceability
- Monitor, log, and audit your environment.
- Implement detective controls that notify and inform you about unexpected environmental occurrences.
5. Automate Security Best Practices
- Use AWS defined of AWS Config or custom rules to ensure your resources comply with best practices.
- Use AWS Security Hub to monitor your security posture
- Use AWS CloudFormation to help your security automation
6. Protect Data in Transit and at Rest
- Only store data you must store, and only as long as necessary.
- Implement data classification procedures and techniques to separate data based on sensitivity, workload, compliance, and retention.
- Encrypt data at rest (S3 bucket encryption, KMS, CloudHSM) and encrypt traffic with SSL/TLS for Data in transit.
7. Keep People Away from Data
- Protecting privacy and confidentiality
- Reducing the Risk of Data Breaches
- Ensuring Compliance with Regulations
- Maintaining Data Integrity
- Protecting Against Social Engineering Attacks
- By automating your processes, you can reduce the risk that comes from human interaction.
Conclusion
In conclusion, as highlighted in the presentation, the importance of security in today’s cloud-driven world cannot be overstated. At NashTech, we provide comprehensive solutions to help clients implement robust cloud security, particularly within AWS environments. For a deeper dive into our Multi-layered Security approach and the strategies we employ, we invite you to reach out to us for more detailed information.


