Image from Internet
Introduction
In today’s digital landscape, websites have become essential tools for businesses, services, and individuals alike. With the increasing reliance on web platforms for daily operations, the security of these websites is more critical than ever. A single vulnerability can lead to severe consequences, including data breaches, loss of user trust, and significant financial and reputational damage. For a website developer and tester, it is crucial to understand the fundamentals of security testing to protect these digital assets effectively.
This post blog will examine prevalent security vulnerabilities that malicious actors exploit to compromise websites, blackmail developers, or steal sensitive user information. Based on that, we will then discuss practical scenarios where these issues frequently arise and a checklist of essential security checks that every website should implement to safeguard sensitive data and maintain the integrity of their online presence.
Frequent Security Threats: Examples from the Real-World

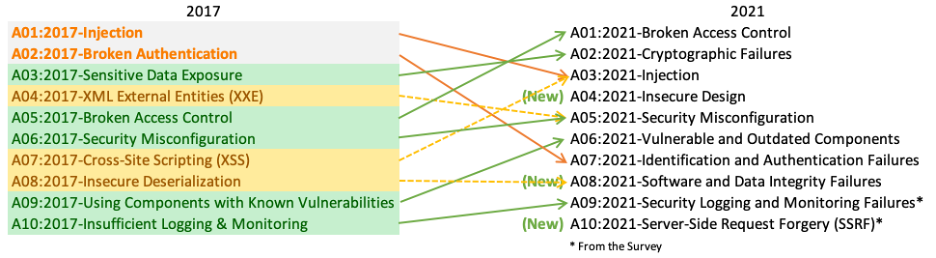
Thus far, numerous website security vulnerabilities have been exploited by hackers across various levels, ranging from straightforward to sophisticated attacks. The following vulnerabilities are particularly prevalent due to their ease of exploitation, frequent occurrence, or severe impact on victims. These flaws are all included in OWASP’s Top 10 List of Web Application Security Risks, recognized by the prestigious software security organization – OWASP.
SQL Injection
Attackers manipulate input fields to inject malicious SQL code into database queries. If the input data is not properly validated or sanitized, the database executes the malicious code. The vulnerabilities that websites often have to allow this type of attack to occur are usually:
- Lack of Input Validation: Not validating or sanitizing user inputs allows malicious SQL code to be injected.
- Dynamic SQL Queries: Using dynamic SQL queries without parameterization makes the application vulnerable.
- Error Messages: Detailed database error messages can provide attackers with information about the database structure.
Hackers can append or alter SQL queries using input fields, such as login forms, search bars, or URL parameters. Additionally, attackers utilize tools like SQLMap to automate the discovery and exploitation of SQL injection vulnerabilities. Common techniques include:
- Union-based SQL Injection: Combining results of two queries to extract data.
- Error-based SQL Injection: Forcing the database to produce error messages revealing structure.
- Blind SQL Injection: Observing the behavior of the application to infer information without receiving direct feedback.
SQL injection attacks can have devastating effects on a website and its database. Attackers can retrieve sensitive information such as personal user data, financial details, and proprietary business information, leading to data breaches. They can also manipulate the database by modifying, deleting, or inserting data, which compromises the integrity of the information stored. Furthermore, attackers may gain administrative control over the database, enabling them to deploy backdoors or malware. In some extreme cases, SQL injection can lead to remote code execution on the server hosting the database, resulting in a full system compromise.
Cross-Site Scripting (XSS)
XSS occurs when attackers inject malicious scripts (usually JavaScript) into web pages viewed by other users. The malicious script is embedded in user inputs, such as comments or search fields. When other users view the infected page, their browsers execute the script, allowing attackers to steal session cookies, redirect users to malicious sites, or perform other actions on their behalf. The vulnerabilities that websites often have to allow this type of attack to occur are usually:
- Insufficient Input Sanitization: Failing to sanitize user inputs allows malicious scripts to be injected.
- Dynamic Content: Websites that generate dynamic content based on user inputs are more prone to XSS.
- Lack of Output Encoding: Not encoding output data makes it easier for scripts to be executed in the browser.
Some types of attacks commonly encountered:
- Stored XSS: The malicious script is permanently stored on the target server, such as in a database, and is served to users when they request the stored content.
- Reflected XSS: The malicious script is reflected off a web server, typically via a URL, and is immediately executed by the user’s browser.
- DOM-based XSS: The vulnerability exists in client-side code rather than server-side, allowing attackers to manipulate the DOM environment of the user’s browser to execute the malicious script.
Cross-Site Scripting (XSS) attacks can result in severe security breaches. Attackers can steal session cookies, enabling them to impersonate users and gain unauthorized access to their accounts. This can lead to further malicious activities, such as data theft and unauthorized transactions. Additionally, attackers can create convincing phishing pages to deceive users into providing their login credentials and other sensitive information. XSS attacks can also deface websites, causing reputational damage, and can be used to distribute malware to users visiting the compromised site, further spreading the impact.
Cross-Site Request Forgery (CSRF)
CSRF exploits the trust that a web application has in a user’s browser, tricking users into executing actions on a different website where they are authenticated. Attackers craft malicious requests and trick authenticated users into executing them, often by embedding the requests in images or hidden forms. These requests are sent from the victim’s browser with the necessary authentication tokens, making them appear legitimate. Some website weaknesses that can be exploited to carry out this type of attack are:
- Lack of Anti-CSRF Tokens: Not implementing anti-CSRF tokens in forms and requests makes the website vulnerable.
- Trust in Browser Requests: Assuming that requests from authenticated browsers are legitimate without additional validation.
- GET Requests for State-Changing Operations: Using GET requests for operations that change state can expose the website to CSRF.
Attackers create a specially crafted URL or form that triggers actions on the target website. Since the request includes the user’s session cookies, the server processes it as an authenticated request. Attackers use social engineering techniques to lure users into clicking malicious links or visiting compromised websites that initiate CSRF attacks. For example, an attacker might send an email with a hidden image tag pointing to a URL on the target site that changes a user’s email address or password.
CSRF attacks can result in unauthorized actions being performed on behalf of authenticated users. Attackers can exploit CSRF vulnerabilities to change account settings, transfer funds, or perform other critical actions without the user’s knowledge. This can lead to significant financial losses, data manipulation, and service disruptions. Additionally, the unauthorized actions performed by attackers can abuse services, such as sending spam emails or posting unauthorized content, causing reputational damage to the website and its users.
Brute Force Attacks
Brute force attacks involve systematically trying different combinations of usernames and passwords until the correct ones are discovered. Attackers use automated tools to try numerous combinations of login credentials. This method relies on the persistence of attackers and the use of weak or common passwords by users such as:
- Weak Password Policies: Allowing users to set weak or common passwords increases vulnerability.
- No Account Lockout Mechanism: Not locking accounts after multiple failed login attempts.
- Predictable Usernames: Using easily guessable usernames (e.g., “admin”).
Automated scripts can try thousands of username-password combinations per second. Attackers often use dictionaries of common passwords and known user credentials, leveraging tools like Hydra and John the Ripper to automate brute force attacks. These tools rapidly cycle through potential combinations, significantly increasing the likelihood of gaining unauthorized access, especially when users employ weak or predictable passwords.
Brute force attacks can result in unauthorized access to user accounts or administrative interfaces, leading to potential data breaches. Once attackers gain access, they can exfiltrate sensitive information, including personal data, financial records, and confidential business information. Unauthorized access can also be leveraged to install malware, create backdoors, or further exploit the system to gain deeper control. The impact of brute force attacks extends to compromised user privacy and trust, as well as potential financial and reputational damage to the targeted organization.
File Upload Vulnerabilities
File upload vulnerabilities occur when attackers exploit flaws in file upload functionalities to upload and execute malicious files (e.g., scripts or malware) on the server. Attackers upload files with malicious code or malware. If the application does not properly validate or restrict the types of files that can be uploaded, these files can be executed on the server, leading to remote code execution or server compromise. The common weaknesses of the website that can be attacked:
- Lack of File Type Validation: Not properly validating or restricting allowed file types.
- Insufficient Content Scanning: Not scanning file contents for malicious code
- Improper Storage of Uploaded Files: Storing uploaded files in a directory accessible for execution without proper permissions.
Attackers can circumvent basic file type checks by altering file extensions, such as changing a .php file to .jpg, to deceive the upload mechanism. Malicious files may also be camouflaged as innocuous ones, like image files, but contain executable code. If these files are uploaded without proper handling and validation, they can be executed. Attackers often target weak file validation and handling processes to upload and execute malicious files, including taking advantage of poorly configured web servers that permit the execution of uploaded files or have inadequate directory permissions. Moreover, the lack of thorough scanning for malicious code in file contents can lead to undetected uploads of harmful scripts, significantly endangering the application’s security.
File upload vulnerabilities can escalate to remote code execution, enabling attackers to run arbitrary code on the server, potentially seizing control of the server and the entire network. This can compromise the server, allowing attackers to alter website content, steal sensitive data, and interrupt services. Attackers might also upload scripts that transfer data from the server to external entities, resulting in data breaches and further exploitation of the compromised system. The repercussions of file upload vulnerabilities are far-reaching, impacting data security, system integrity, and the trustworthiness of the web application involved.
Enhancing Web Application Security: Effective Methods and Techniques
To effectively mitigate the discussed vulnerabilities, during the software development life cycle, emphasis should be placed on security testing using manual testing techniques combined with automated tools. Manual testing plays an important role in identifying complex security flaws that automated scanners may miss. Here are some essential methods and techniques to enhance web application security:

Input Validation and Sanitization: Input validation remains a cornerstone in preventing numerous types of attacks, including SQL injection and Cross-Site Scripting (XSS). Developers should rigorously validate and sanitize all user inputs to ensure they conform to expected formats and do not contain malicious content. For instance, validating email addresses to match a standard format and encoding special characters (such as <, >, and &) can prevent XSS attacks by neutralizing malicious scripts embedded in user inputs.
Secure File Uploads: Implementing robust security measures during file uploads is critical to prevent file upload vulnerabilities, such as allowing malicious scripts to be executed on the server. Developers should adopt a defense-in-depth approach, incorporating multiple layers of security:
- Extension Validation: Verify file extensions after decoding the file name to prevent attackers from bypassing basic checks by altering file extensions. Restrict uploads to business-critical file types only and blacklist potentially harmful extensions.
- File Uploads Validation: While users may provide a content-type for uploaded files, this cannot be trusted as it can be easily spoofed. Implement robust content scanning mechanisms to detect and block files containing malicious or unauthorized content.
- Proper Storage and Permissions: Store uploaded files in a secure directory with limited execution permissions to mitigate the risk of remote code execution. Ensure files are accessible only to authorized users based on appropriate role-based access controls (RBAC).
Password Policy and Brute Force Protection: To prevent the risk of Brute Force attacks, some of the solutions below can be considered
- Use Strong Passwords: Enforce policies that mandate strong passwords, combining uppercase and lowercase letters, numbers, and special characters.
- Limit Login Attempts: Implement mechanisms to restrict the number of failed logins attempts per user session. After reaching the limit, temporarily lock or throttle login attempts from the same IP address to thwart brute force attacks.
- Use Two-Factor Authentication (2FA): Enhance authentication security by implementing 2FA, requiring users to verify their identity using a second factor (e.g., SMS code, authenticator app) in addition to their password.
- Use CAPTCHAs or Unique Login URLs: Integrate CAPTCHA challenges to differentiate between human users and automated bots attempting to brute force credentials. Consider generating unique login URLs or tokens for each session or user group to add an additional layer of security against automated attacks.
Session Management: Effective session management is crucial to prevent session hijacking and unauthorized access
- Token-Based Sessions: Utilize tokens with configurable properties (e.g., expiration date, usage constraints) for session management instead of exposing session IDs in URLs or relying solely on cookies.
- Secure Transmission: Ensure session tokens are transmitted over secure channels (e.g., HTTPS) to prevent interception by attackers monitoring network traffic.
- Session Expiry and Revocation: Implement mechanisms to expire sessions after a period of inactivity and provide users with the ability to revoke active sessions from their account settings.
Conclusion
With cyber threats and attacks becoming more sophisticated and frequent in the current landscape, developers must prioritize the safety of user information and always follow best practices to reduce minimize these risks. By staying informed continuously and investing in security solutions, development team can protect data integrity and maintain user trust. Security testing is more than just a task—it’s essential for protecting web applications.
Reference
- Image from the internet
- Top 10 Web Application Security Risks – OWASP Top Ten | OWASP Foundation


