When building websites or applications, it’s crucial to make sure they’re safe from cyber threats. That’s where security testing comes in. OWASP ZAP, also known as Zed Attack Proxy, is a powerful tool that helps us test for security issues.
Ensuring that our applications are safe from potential threats is non-negotiable. This is where OWASP ZAP, or Zed Attack Proxy, steps in as a formidable ally. It’s a powerful tool that helps us uncover vulnerabilities and strengthen our web applications. However, understanding the results it generates is equally crucial. In this blog post, we’ll learn Best Practices and Tools for ZAP Security Testing Results.
Best Practices for Interpreting ZAP Security Testing Results
OWASP ZAP (Zed Attack Proxy) plays a pivotal role in safeguarding web applications by uncovering potential vulnerabilities. However, comprehending the results it generates is vital for effective security analysis. This article outlines best practices for interpreting ZAP security testing outcomes, ensuring a thorough evaluation of potential risks.
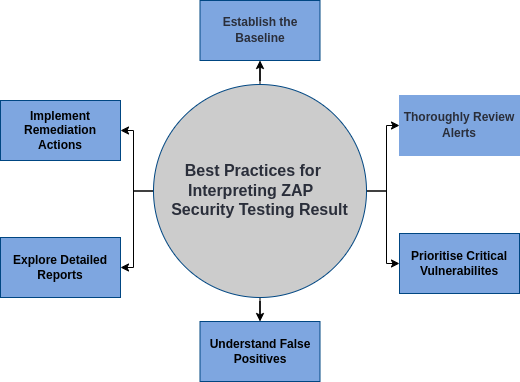
1. Establish a Baseline:
Begin by establishing a baseline for your application’s normal behavior. This serves as a reference point for identifying deviations during security testing. Understanding the expected state of your application allows for more accurate identification of potential vulnerabilities.
2. Thoroughly Review Alerts:
ZAP generates alerts for various security issues it identifies during testing. Take the time to thoroughly review each alert. Analyze the type of vulnerability it represents and consider its potential impact on your application. This detailed examination ensures that no potential risks go unnoticed.
3. Prioritise Critical Vulnerabilities:
Focus on addressing critical vulnerabilities first, as they have the highest potential for exploitation. These may include severe issues like remote code execution or exposure of sensitive data. Tackling these high-priority vulnerabilities promptly is crucial for safeguarding your application.
4. Understand False Positives:
Automated security testing tools, including ZAP, may occasionally trigger false alarms. These false positives can lead to unnecessary concern. It is essential to investigate and verify each alert to distinguish between actual vulnerabilities (true positives) and non-issues (false positives). This distinction ensures that resources are allocated efficiently for resolving genuine security concerns.
5. Explore Detailed Reports:
ZAP provides detailed reports that offer a wealth of information about identified vulnerabilities. Dive into these reports to gain deeper insights into the nature of each issue. The reports categorize vulnerabilities, provide descriptions, and suggest possible remediation strategies. This information empowers you to make informed decisions about how to address the identified security risks.
6. Implement Remediation Actions:
Once vulnerabilities are identified, take appropriate remediation actions. This could involve code fixes, configuration adjustments, or implementing additional security measures. Regularly retest the application to ensure that the remediation actions effectively mitigate the identified risks.
Best Tools for Interpreting ZAP Security Testing Results
Here we have some of the best tools available for interpreting ZAP security testing outcomes, providing invaluable insights into potential risks.
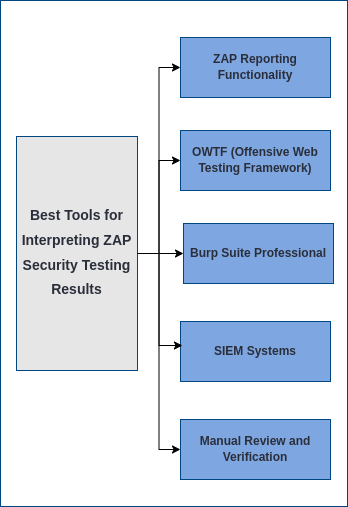
1. ZAP Reporting Functionality:
ZAP itself offers a robust reporting feature that allows users to generate reports in various formats, including HTML and XML. These reports provide a structured overview of the testing results, making it easier to share and analyze with your team. The simplicity and comprehensiveness of ZAP’s built-in reporting make it an essential tool for any security professional.
2. OWTF (Offensive Web Testing Framework):
OWTF is a versatile security framework that integrates various security tools, including ZAP. It provides additional features specifically designed for interpreting ZAP results. OWTF’s capabilities extend beyond traditional security testing, making it a valuable tool for security professionals looking to enhance their testing capabilities.
3. Burp Suite Professional:
While Burp Suite is primarily known for its web application scanning capabilities, the professional version includes advanced reporting features that complement ZAP’s capabilities. Burp Suite’s extensive reporting options provide detailed insights into vulnerabilities, allowing security professionals to prioritise and address them effectively.
4. Security Information and Event Management (SIEM) Systems:
For larger organizations or those with complex security requirements, SIEM systems like Splunk or ELK Stack can be invaluable. These systems allow you to aggregate and analyze ZAP testing results at scale, providing a centralized platform for monitoring security events across your applications. SIEM systems offer the capability to correlate data from multiple sources, providing a holistic view of your application security.
5. Manual Review and Verification:
While automated tools are powerful, manual review and verification remain critical components of interpreting ZAP results. Experienced security professionals can provide valuable context and insight into identified vulnerabilities, helping to prioritise and address them effectively.
Summary :
Effectively interpreting ZAP security testing results is crucial for identifying and mitigating potential risks in web applications. By following best practices and utilising the right tools, security professionals can ensure that their applications are secure and resilient against cyber threats. Remember, security is an ongoing process, and regular testing and analysis are paramount to maintaining a robust security posture. With ZAP and these best practices, you’ll be well-equipped to safeguard your applications in today’s ever-evolving threat landscape.