We will explore the proper handling of sensitive information in the .NET development environment. Specifically, we will focus on protecting secrets used during development. These secrets refer to sensitive information used in the development environment.
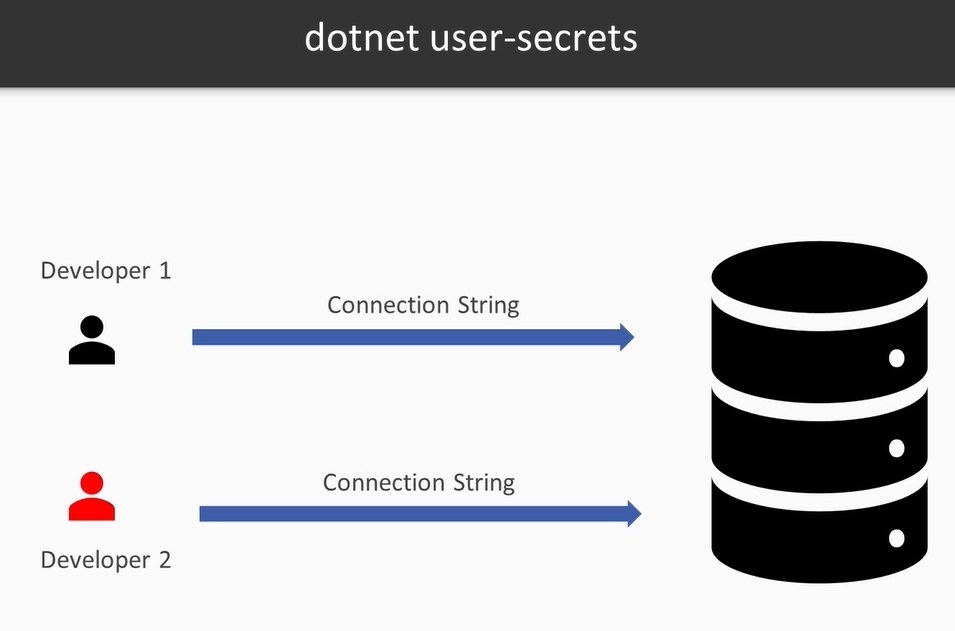
Consider a scenario where two developers are working on a project, each requiring their own dedicated passwords to connect to the database. It is essential for each developer to prevent the sharing of these passwords during development. Fortunately, .NET offers a solution called “.NET Secrets” to address this. Let’s delve into how it works.
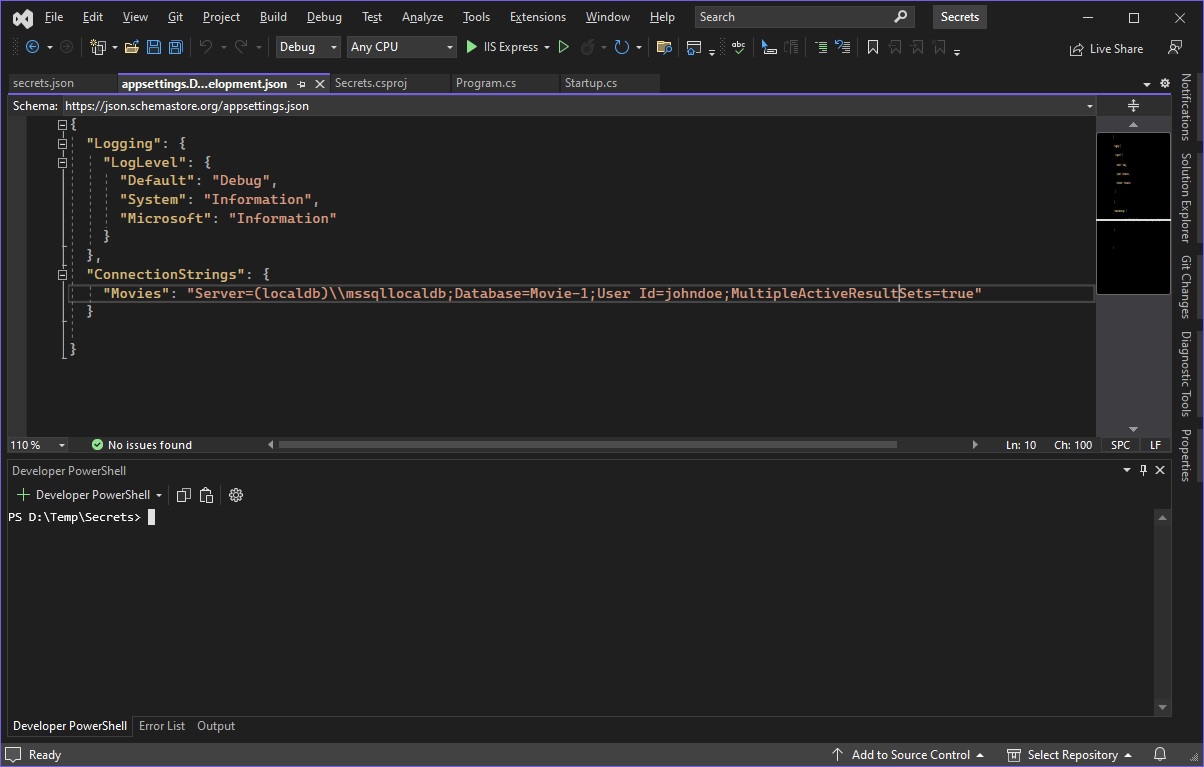
In this example, we have a simple web application with a connection string named “Movies” stored in the appsettings.Development.json file. However, the connection string only contains the UserID and does not include the password. Here’s the connection string: "Server=(localdb)\\mssqllocaldb;Database=Movie-1;User Id=hieunguyenc;MultipleActiveResultSets=true".
While this connection string could have been parameterized, for simplicity’s sake, we will focus on keeping the password as a secret. To achieve this, we need to execute the “dotnet user-secrets init” command in the Terminal window. This command modifies the project file by adding a GUID named “UserSecretsId”. Running this command to create the GUID, and then we need to check the project file (.csproj).
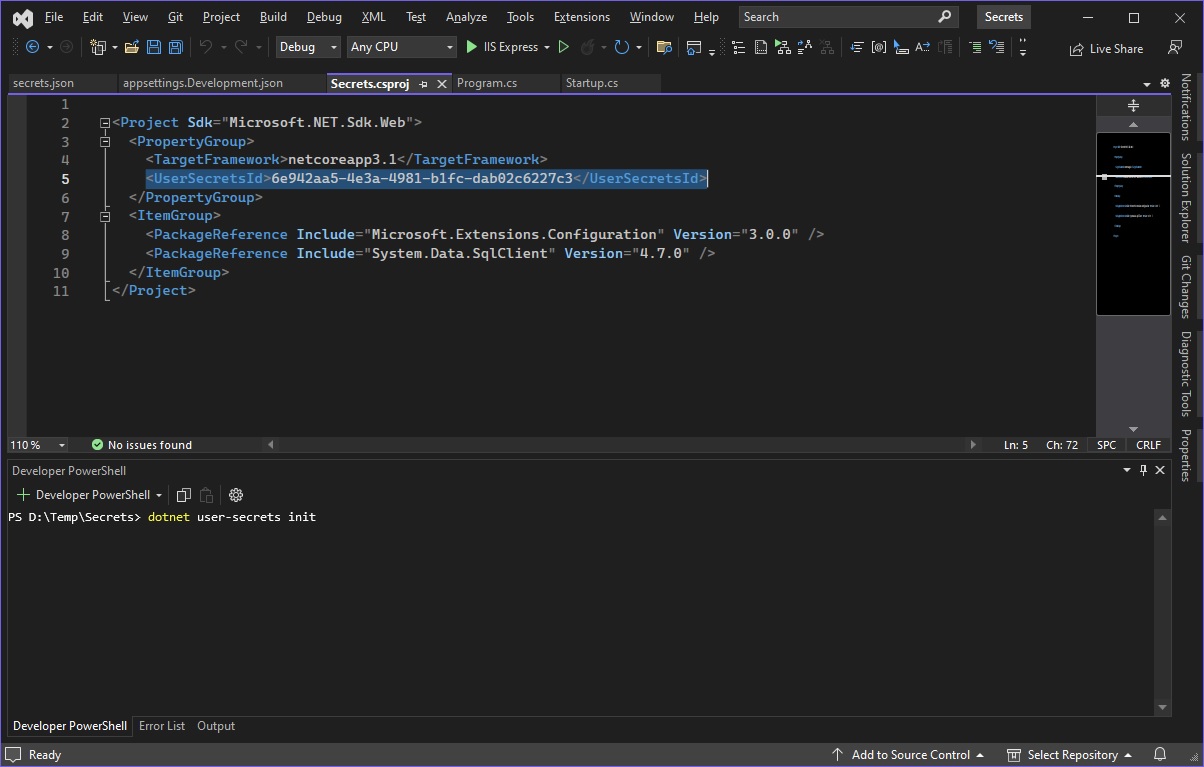
Upon inspecting the project file, you will notice that the UserSecretsId has been added to it. This sets the stage for adding secret information such as the database password. To add the secret, we use the “dotnet user-secrets” command and set the relavant key-value pair. For example: dotnet user-secrets set “DbPassword” “pass123”. In this case, the key is “DbPassword” and the value is “pass123”. You can set other keys and their values, such as the UserID, in the same manner.
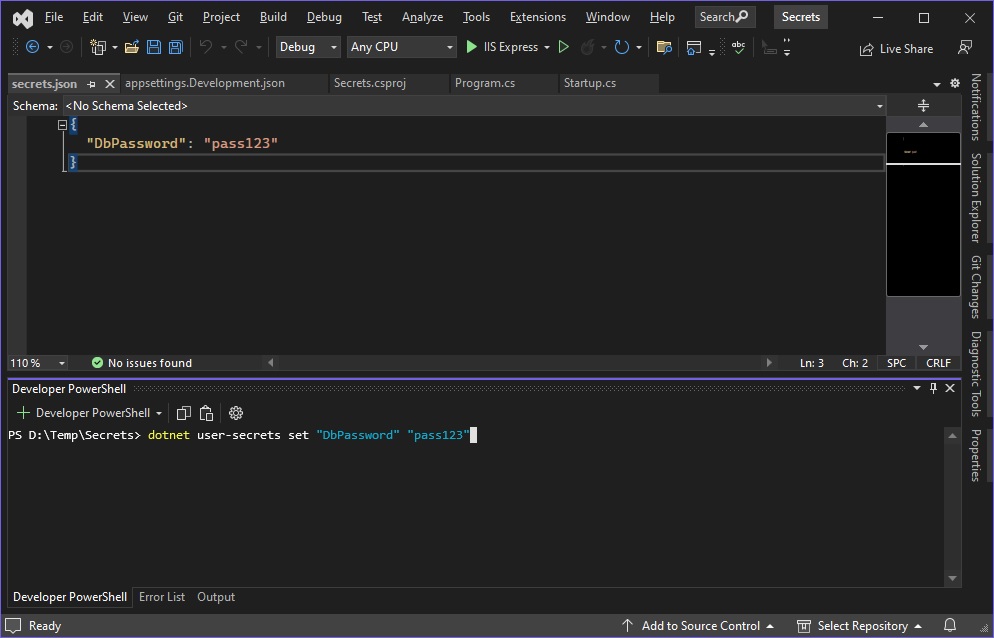
Another approaching to modify values in the Secrets file is to right-click on the project in the Solution Explorer panel and choose “Manage User Secrets”. This option saves the secrets to a secret store located under your profile folder, typycally at “C:\Users<UserName>\AppData\Roaming\Microsoft\UserSecrets<UserSecretsId>“. Please note that this storage is solely intended for development purposes. It is not encrypted and should not be used for sharing sensitive information.
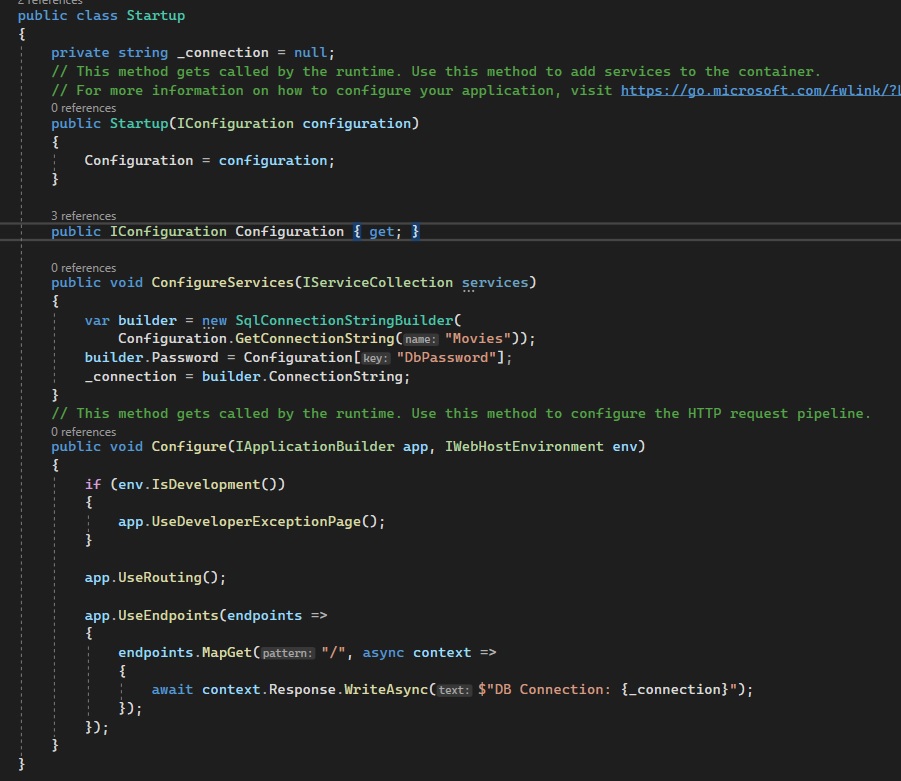
To utilize the secrets, we make use of the ConfigureService() method in the Startup program. In this method, we can observe the use of a SqlConnectionStringBuilder. If you’re not using a SQL connection string builder, that’s still fine; the key part is accessing the secret value via the Configuration extension using the “DbPassword” key. We retrieve the secret value using Configuration[“DbPassword”] and set it as the password in the builder.Password field.
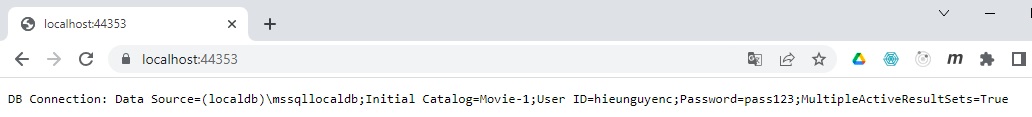
Running the application demonstrates that the password appears in the correct position, even if it is not defined in the configuration. This serves as a good example of how to manage secrets in your development environment.
For more detailed information about the .NET Secrets extension, please refer to the link:
https://learn.microsoft.com/en-us/aspnet/core/security/app-secrets?view=aspnetcore-7.0&tabs=windows
