Every application nowadays has some form of sensitive data that needs to be protected. Such data in the wrong hands can lead to catastrophic failures. Avoiding such failures is extremely important with the advancement in technology. Security testing can be performed on your web application to find security gaps so that your data is safe in production from attackers.
Before we see how to detect such security risks, let us first look at some of the common security vulnerabilities that you might find within your application. We will cover a few of the most common issues that people face when it comes to security. Later, we will try to see how these can be detected effectively with testing methods.
Common Security Vulnerability
To give a brief about what we mean by common security vulnerabilities, they are weaknesses in software, hardware, or systems that can be exploited by malicious attackers to compromise the confidentiality, integrity, or availability of data or functionality. Detecting these vulnerabilities is crucial to maintaining the security of systems. OWASP provides us with an excellent list of the top 10 vulnerabilities if you want to read in detail about these issues. For now, we will focus on a few of the most common issues.
1. Injection Attacks
These include attacks such as SQL injection and command injection. They usually occur when an attacker injects malicious code (SQL, OS commands, etc.) into an application, often through input fields. Following is an example of such an attack :
Your application takes some user input, say username and puts it into an SQL query to retrieve the information for the specified username from the database. The query would look like this :-
user_input = request.get("username")
query = "SELECT * FROM users WHERE username = '" + user_input + "';"
result = execute_sql_query(query)Suppose a user adds the following in the place of a valid username : ‘ OR ‘1’=’1. The query would look then like :-
SELECT * FROM users WHERE username = '' OR '1'='1';Since ‘1’=’1′ is always true, this modified query would retrieve all the rows from the users table, effectively bypassing any legitimate authentication or filtering mechanisms
To detect such injection attacks manually, we can look at the following methods :-
- Input validation: Ensure inputs are properly sanitized and validated.
- Use parameterized queries to prevent SQL injection.
- Use security mechanisms that block or log suspicious patterns.
2. Cross-Site Scripting
Cross-Site Scripting (XSS) is a type of security vulnerability where attackers inject malicious scripts into web applications that are then executed by unsuspecting users in their browsers. These scripts can steal sensitive information, manipulate user sessions, deface websites, or perform other malicious actions. XSS vulnerabilities arise when an application does not properly validate or sanitize user input before rendering it on a webpage. These are the three main types of XSS attacks:
- Stored (Persistent) XSS: Malicious scripts are permanently stored on the target server, and every user who views the compromised page becomes a potential victim.
- Reflected (Non-Persistent) XSS: Malicious scripts are embedded in a URL or form input and then reflected back to the user in the response from the server. The attack is typically targeted at a specific victim and requires the victim to click on a malicious link.
- DOM-based XSS: The vulnerability arises within the Document Object Model (DOM) of a web page. Malicious scripts manipulate the DOM elements on the client side, often without sending data to the server.
Let us look at an example of one such attack:-
Suppose you have a search page on a website that takes a user’s query and displays it in the search results without proper input validation:
<!-- Search Page -->
<form action="/search">
<input type="text" name="query">
<input type="submit" value="Search">
</form>If a user enters the following as their search query: <script>alert(‘XSS’);</script>
The resulting URL would look like:
https://example.com/search?query=<script>alert('XSS');</script>As a result, the browser executes the embedded script, causing an alert box to pop up with the message “XSS.”
To detect such injection attacks manually, we can look at the following methods :-
- Input validation: Validate and sanitize user input.
- Use CSP headers to restrict the source of exe scripts.
3. Cross-Site Request Forgery
Cross-Site Request Forgery (CSRF), also known as XSRF, is a type of security vulnerability in web applications where an attacker tricks a user into unknowingly making an unwanted action on a different site where the user is already authenticated. The attack takes advantage of the fact that a user’s browser will automatically include the user’s credentials (such as session cookies) when making requests to the target site. Let us look at an example of such an attack:-
Suppose you have an online banking application that allows users to transfer money to other accounts using a simple HTTP GET request. The application uses the following URL for transferring funds:
https://bank.example/transfer?amount=100&destinationAccount=attackerAccountAn attacker sets up a malicious website and tricks the victim into visiting it. On the attacker’s website, there’s an image tag that has the URL of the money transfer request as its “src” attribute:
<img src="https://bank.example/transfer?amount=100&destinationAccount=attackerAccount">Now, if the victim is already authenticated on the bank’s website and visits the attacker’s website, the browser will automatically send a request to the bank’s server to transfer $100 from the victim’s account to the attacker’s account. Since the browser includes the victim’s session cookies, the bank’s server assumes the request is legitimate.
To detect such injection attacks manually, we can look at the following methods :-
- Implement anti-CSRF tokens in forms.
- Check the “Origin” or “Referer” header to ensure requests are from the same origin.
Detect Security Vulnerabilities Using OWASP ZAP
Now that we have looked at three common security vulnerabilities, let us see how we can detect these with the help of a security testing tool. Perhaps the most widely used security test tool, OWASP ZAP can be used to identify and fix vulnerabilities in web applications during the development and testing stages. It can also be integrated with Selenium to automate your security testing.
Before we start detecting vulnerabilities with OWASP ZAP, let us fulfil some prerequisites for using this security test tool :
Prerequisites
- You have installed OWASP Zap on your machine. You can use the following URL to install it based on your requirements – OWASP Zap installation.
How to start the scanning with OWASP ZAP to detect vulnerabilities?
The vulnerabilities that are added above can be detected easily with OWASP ZAP scanning. Let us look at the steps that we need to follow to do the same.
Step 1: Configure your browser to use ZAP as a proxy
We will use Firefox for this demo. You can choose another browser of your choice.
1. Open Firefox and click on the menu icon (three horizontal lines) in the top-right corner.
2. Select “Options” or “Preferences,” depending on your Firefox version.
3. In the left sidebar, click on “General” (Firefox Options) or “Privacy & Security” (Firefox Preferences).
4. Scroll down to the “Network Settings” section.
5. Click the “Settings” button next to “Configure how Firefox connects to the Internet.”
6. In the Connection Settings window that appears, select the “Manual proxy configuration” option.
7. In the “HTTP Proxy” field, enter localhost and the port number ZAP is listening on (usually 8080 by default).
8. Click “OK” to save the proxy settings
Step 2 : Launch OWASP ZAP and click on browser
Open your OWASP ZAP and click on the browser that you have chosen to proxy through ZAP
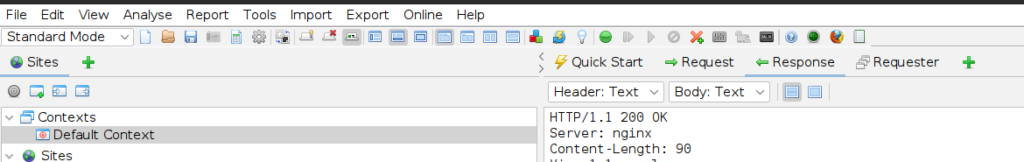
Step 3: Go to the “Sites” tab in ZAP and right click on the website and choose “Attack” > “Active Scan”
Step 4: After the scan completes, review the results in the “Alerts” tab

Featured image source : https://www.rutter-net.com/blog/how-to-conduct-a-security-vulnerability-assessment


