In modern software architectures, Forward Proxy vs Reverse Proxy is essential for managing network traffic, improving security, and optimizing performance. Though both proxies have crucial roles in different scenarios, they are often misunderstood. This blog will explore the key differences between Forward Proxy vs Reverse Proxy, how to implement them in software architectures, and their common use in cloud environments.
What is a Forward Proxy?

A Forward Proxy is an intermediary between a client and the external Internet. When a client, such as a browser or device, requests to access an external resource (like a website), the forward proxy processes the request before passing it on to the destination server. It effectively hides the client’s identity from the server.
Key Functions of a Forward Proxy:
- Client Anonymity: Forward proxies mask the client’s IP address from the target server.
- Access Control: They can restrict or filter outbound requests from clients, and they are often used in corporate networks to control internet access.
- Caching: Forward proxies can cache frequently accessed web resources, reducing bandwidth usage and improving access times.
- Security: Proxies can block malicious requests and prevent users from accessing unsafe or restricted websites.
Common Use Cases:
- Corporate Networks: Restrict employee internet access and log outbound traffic.
- Content Filtering: Used in educational institutions to block specific categories of websites.
- Bypassing Geolocation Restrictions: Users can mask their IP address to access content that might be restricted in their region.
What is a Reverse Proxy?
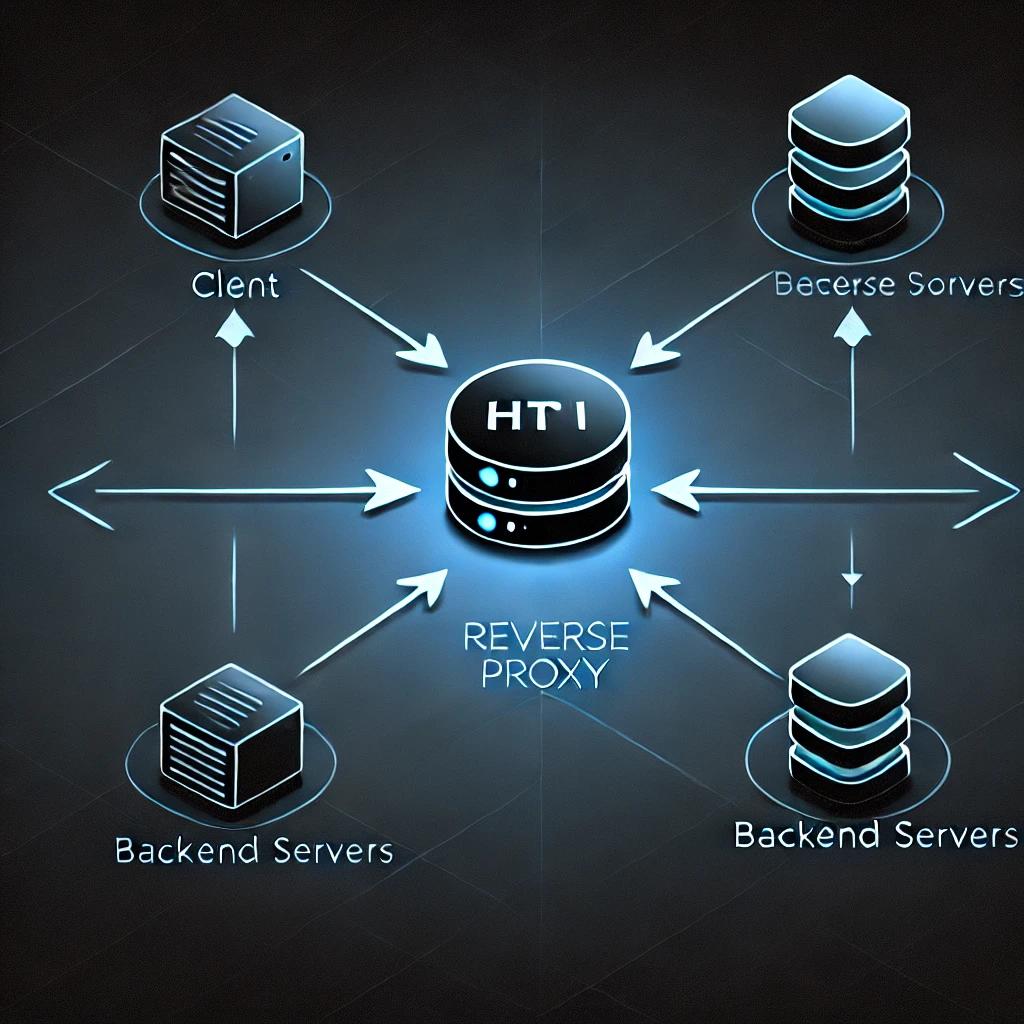
A reverse proxy, on the other hand, sits in front of web servers and handles requests on behalf of those servers. When a user requests a website, the reverse proxy intercepts it, processes the request, and forwards it to the appropriate server behind the proxy. The user is unaware of which server actually fulfills the request.
Key Functions of a Reverse Proxy:
- Load Balancing: Distributes incoming client requests across multiple servers to ensure no single server is overwhelmed.
- SSL Termination: A reverse proxy can handle SSL encryption and decryption, offloading this task from backend servers.
- Caching: It caches content like static files to reduce the load on the backend servers and improve performance.
- Security: Reverse proxies shield backend servers from direct exposure to the public internet, protecting them from attacks.
Common Use Cases:
- Load Balancing: Distributing traffic to multiple servers in web applications.
- Security: Hiding backend servers behind a proxy to prevent direct access.
- Content Delivery Networks (CDNs): CDNs use reverse proxies to cache content closer to users for faster delivery.
Forward Proxy vs Reverse Proxy: Key Differences
| Feature | Forward Proxy | Reverse Proxy |
|---|---|---|
| Client/Server Focus | Acts on behalf of the client | Acts on behalf of the server |
| Location | Placed between client and external internet | Placed between external clients and servers |
| Primary Use Case | Hide client identity and filter outbound traffic | Hide server identity and optimize inbound traffic |
| Common Usage | Corporate networks, content filtering | Load balancing, SSL termination, security |
The fundamental difference lies in who the proxy is acting for. A forward proxy is designed to represent the client, while a reverse proxy represents the server.
Implementing Proxies in Software Architecture
Incorporating proxies into a software architecture depends on the system’s specific requirements, such as security, performance, and scalability.
Forward Proxy Implementation: Key Considerations
- Client-Side Configuration: To begin with, the client (browser or device) must be configured to use the forward proxy. Typically, this configuration is applied in corporate networks, where proxy settings are enforced through network policies.
- Security Considerations: The proxy must be secure, as it becomes a critical point in the network infrastructure. Configuring firewalls and access control lists (ACLs) is essential.
- Caching: Caching at the proxy level can drastically reduce bandwidth consumption for systems with significant outbound internet traffic.
Popular Forward Proxy Tools:
- Squid: A caching and forwarding proxy widely used in enterprise environments.
- Privoxy: A non-caching proxy focused on privacy.
Reverse Proxy Implementation: Key Considerations
- Server-Side Configuration: Reverse proxies require careful configuration on the server side, ensuring they can correctly distribute traffic and handle tasks like SSL termination or load balancing.
- Scalability: Reverse proxies are commonly used to scale web applications. For instance, in a microservices architecture, a reverse proxy can route traffic to the correct microservice.
- Security and Encryption: SSL termination at the reverse proxy reduces the overhead on backend servers. However, it also requires a secure setup of SSL certificates and appropriate handling of encrypted traffic.
Popular Reverse Proxy Tools:
- Nginx: A highly efficient reverse proxy server known for its performance and scalability.
- HAProxy: A load balancer and reverse proxy widely used in high-availability environments.
Forward Proxy vs Reverse Proxy: in Cloud Architecture
Forward and Reverse proxies are essential in cloud environments for managing traffic, enhancing security, and optimizing costs.
What is Forward Proxy in Cloud?
Cloud-based setups often use forward proxies to enforce internet access control policies. For example, organizations using AWS or Google Cloud can route outbound traffic through a forward proxy to control which services or websites their applications can access. Additionally, cloud providers often integrate with proxy services for logging and monitoring outbound requests, improving network security and visibility.
How about Reverse Proxy?
Reverse proxies are more commonly used in cloud architectures to handle incoming traffic. In cloud-native applications, services like AWS Elastic Load Balancer or Azure Application Gateway act as reverse proxies, distributing traffic across multiple instances to ensure scalability and high availability.
- Cloud Load Balancers: Services like AWS Elastic Load Balancing (ELB) or Google Cloud Load Balancer often function as reverse proxies, balancing traffic and shielding backend instances from direct internet access.
- Security and SSL Termination: Reverse proxies in the cloud often manage SSL termination, offloading encryption tasks from backend servers and centralizing SSL certificate management.
Proxy Considerations in Cloud Environments:
- Scalability: Cloud environments demand that proxies can scale efficiently with the application. Cloud-based proxies, like AWS ELB, automatically adjust their capacity based on traffic loads.
- Security: Both forward and reverse proxies can enhance security by restricting traffic flow, filtering unwanted requests, and protecting backend resources.
Conclusion about Forward Proxy vs Reverse Proxy:
Both Forward and Reverse proxies play vital roles in modern software architectures, though they serve different purposes. While forward proxies manage outbound traffic from clients to external networks, reverse proxies handle inbound traffic to servers, improving scalability, security, and performance.
In cloud environments, proxies are indispensable for ensuring efficient resource use, managing security, and optimizing performance. Whether you’re looking to secure client traffic with a forward proxy or scale your infrastructure with a reverse proxy, understanding the differences and implementation strategies is key to building resilient, high-performing systems.
Reference
- What is a Forward Proxy? – Cloudflare
- What is a Reverse Proxy? – Cloudflare
- Forward Proxy vs Reverse Proxy – Nginx
- Understanding Forward and Reverse Proxies – Imperva
- Reverse Proxy Guide – Nginx
- Forward Proxy Configuration – Squid Proxy
- What is a Proxy Server? – AWS
- How Forward and Reverse Proxies Work – Akamai
- Understanding Reverse Proxy with Load Balancing – HAProxy
- Proxy Server Use Cases – DigitalOcean
- Forward Proxy and Reverse Proxy Differences – Varonis
- What is a Forward Proxy? – Palo Alto Networks


