Introduction:
In today’s interconnected digital landscape, collaboration and sharing are central to software development. However, with this openness comes the responsibility of safeguarding sensitive information, such as passwords and API tokens. Despite being indispensable for version control and collaboration, Git repositories can inadvertently harbor unintended secrets. Fortunately, tools like GitLeaks offer an effective solution by providing the means to scan for and mitigate such risks. So let’s begin the blog Getting started with Gitleaks.
What is GitLeaks?
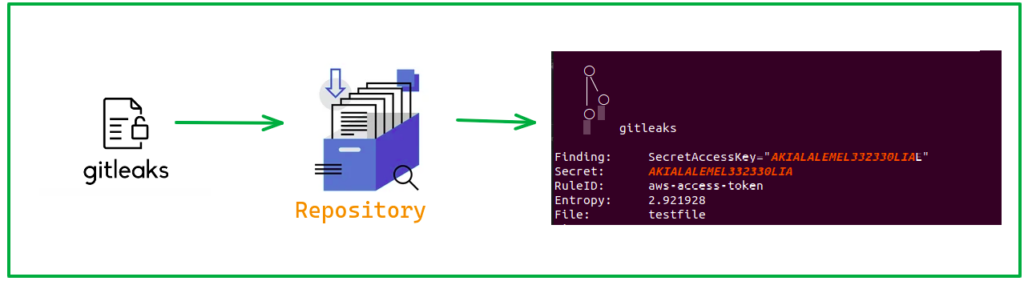
GitLeaks is an open-source tool tailored to scan Git repositories for potential leaks of sensitive information. It operates by utilizing regular expressions to search for patterns indicative of common credentials, including passwords, API keys, and other sensitive data, within the repository’s codebase. By integrating GitLeaks into your development workflow, you gain the ability to proactively identify and address potential security vulnerabilities before they escalate into more significant issues.
How does GitLeaks work?
Utilizing GitLeaks involves setting up a rule file containing predefined rules for detecting sensitive credentials, such as passwords, API tokens, and client keys. These rules are defined using regular expressions to match specific patterns indicative of sensitive information.
Why use GitLeaks?
When leveraging Git for version control, our code becomes visible to everyone involved in the project. Inadvertently including sensitive information within our code poses a significant risk, as it can be accessed by unauthorized parties. GitLeaks serves as a crucial tool for early detection, allowing us to secure our data and ourselves against potential breaches before they occur.
Demo:
-
-
-
Istallation:
You can install GitLeaks via the provided GitHub releases(https://github.com/gitleaks/gitleaks/releases) link or utilize the Docker image available at Docker Hub(https://hub.docker.com/r/zricethezav/gitleaks) . Additionally, you’ll need to create a
.gitleaks.tomlfile to configure GitLeaks with specific rules for detecting sensitive information. Below is an example configuration file: .gitleaks.toml
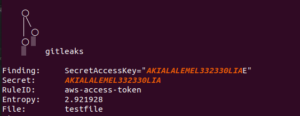
[[rules]] id = "aws-access-token" description = "Identifies patterns indicative of AWS credentials, preventing unauthorized cloud resource access and potential data breaches." regex = '''(?:A3T[A-Z0-9]|AKIA|ASIA|ABIA|ACCA)[A-Z0-9]{16}'''keywords = [“akia”, “asia”, “abia”, “acca”]
#This example rule detects AWS access tokens within the codebase. -
Test File:
Create a test file and paste the following content:
SecretAccessKey="AKIALALEMEL332320OILE" -
Running GitLeaks:
To scan the repository, you can use the command:
gitleaks detect -v –config=.gitleaks.toml –no-git
Alternatively, if Docker is installed on your system, you can use:
docker run -v ${PWD}:/path zricethezav/gitleaks:latest detect –no-git —source=“/path” -v –config=“/path/.gitleaks.toml”
-
-