Introduction: In today’s digital landscape, managing secrets and sensitive data is of utmost importance to protect critical information and maintain data integrity. Ansible, a powerful automation tool, provides Ansible Vault as a secure solution for managing and encrypting secrets within playbooks, inventory files, and variable files. In this blog, we will explore how to effectively manage secrets and sensitive data using Ansible Vault.
Step 1: Creating an Encrypted Vault
To start managing secrets with Ansible Vault, you need to create an encrypted vault file. The vault file acts as a secure container for storing sensitive data. Use the following command to create a new encrypted vault file:
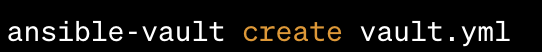
This command will prompt you to set a password for encrypting the vault file. Choose a strong password and keep it safe as it will be required to decrypt and access the vault later.
Step 2: Editing the Vault Content
Once the vault file is created and encrypted, you can edit its content using the following command:
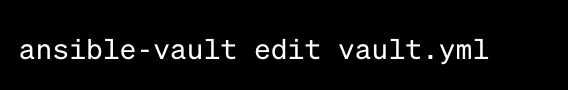
This command will open the vault file in your default text editor. Add the secrets and sensitive data in key-value pairs or any desired format. Save the file after adding the necessary information.
Step 3: Encrypting Existing Files
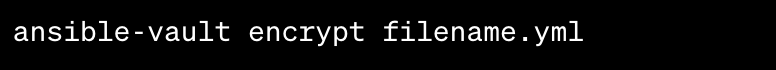
This command will encrypt the file, making it inaccessible without the decryption password. Make sure to keep a backup of the original unencrypted file before encryption.
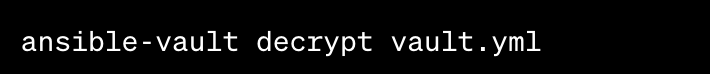
Step 5: Running Playbooks with Vault To use the secrets stored in the vault within your playbooks, you need to provide the decryption password during playbook execution. Use the following command to run a playbook that uses an encrypted vault:
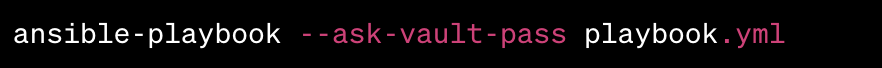
This command will prompt you to enter the decryption password for the vault file. Once provided, Ansible will decrypt the vault and use the secrets within the playbook.
Step 6: Encrypting Variables within Playbooks In addition to encrypting entire files with Ansible Vault, you can also encrypt specific variables within your playbooks. Use the ansible-vault encrypt_string command to encrypt a specific variable:
ansible-vault encrypt_string 'my_secret_value' --name 'my_secret_variable'
This command will output the encrypted string that you can directly use in your playbooks. Replace the original variable value with the encrypted string, ensuring the sensitive data remains secure.
Sample Ansible Code Snippet:
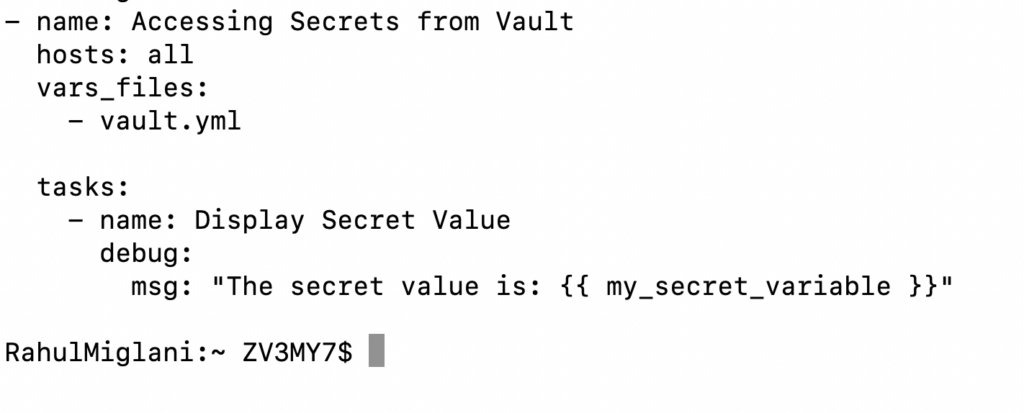
Conclusion: Managing secrets and sensitive data is a critical aspect of maintaining security in your automation workflows. Ansible Vault provides a straightforward and secure solution for encrypting and managing secrets within playbooks and variable files. In this guide, we have covered the steps involved in creating an encrypted vault, editing its content, encrypting existing files, decrypting the vault, running playbooks with vault, and encrypting variables within playbooks. By leveraging Ansible Vault, you can protect your sensitive data and ensure secure automation practices.


