SECURITY IN MOBILE APPLICATION
Mobile security in mobile application is the practice of protecting mobile apps from external threats such as malware, phishing, tampering, reverse engineering, and data breaches. It focuses on ensuring the confidentiality, integrity, and availability of the data and functionality of the apps, as well as the privacy and identity of the users.
We need mobile security because mobile devices are increasingly used for various personal and professional purposes, such as communication, banking, shopping, entertainment, education, health, etc. These devices store and transmit a lot of sensitive or confidential data, such as passwords, credit card numbers, photos, contacts, messages, emails, etc. that can be valuable or harmful if accessed by unauthorized parties.
Mobile security helps to protect our devices and data from various types of threats and risks, such as malware, phishing, data breaches, device theft or loss, network spoofing, etc…
WHAT KINDS OF MOBILE APPLICATION NEED SECURITY?
- Banking and financial applications: These applications allow users to manage their money, make transactions, pay bills, etc.
- Healthcare and medical applications: These applications provide users with access to health records, prescriptions, appointments, etc.
- E-commerce and retail applications: These applications enable users to shop online, browse products, make purchases, etc.
- Gaming and entertainment applications: These applications offer users various forms of fun and leisure activities, such as playing games, watching videos, listening to music, etc.
- Social media and communication applications: These applications allow users to connect with others, share messages, photos, videos, etc.
HOW DO WE APPLY SECURITY?
There are many ways to improve security in mobile application. But to apply it effectively, we need a standard which is accepted and used widely by many companies. This is OWASP.
OWASP stands for Open Web Application Security Project. It is a nonprofit foundation that promotes application security by publishing resources, education, and training. This also develops standards for mobile security called OWASP MASVS (Mobile Application Security Verification Standards).
The OWASP MASVS 2.0.0 is already available at v2.0.0. It has 7 categories of security requirements for mobile apps, which are:
- MASVS-STORAGE: Secure storage of sensitive data on a device (data-at-rest).
- MASVS-CRYPTO: Cryptographic functionality used to protect sensitive data.
- MASVS-AUTH: Authentication and authorization mechanisms used by the mobile app.
- MASVS-NETWORK: Secure network communication between the mobile app and remote endpoints (data-in-transit).
- MASVS-PLATFORM: Secure interaction with the underlying mobile platform and other installed apps.
- MASVS-CODE: Security best practices for data processing and keeping the app up to date.
- MASVS-RESILIENCE: Resilience to reverse engineering and tampering attempts.
Besides that, OWASP also define level of security:
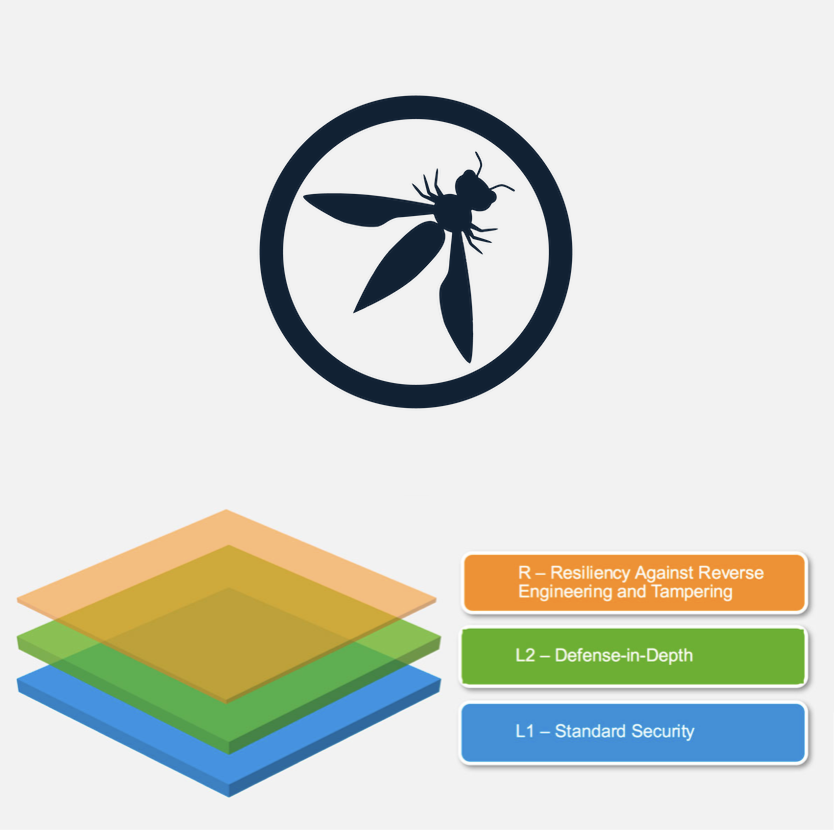
- MASVS-L1: Standard Security
- A mobile app that achieves MASVS-L1 adheres to mobile application security best practices. It fulfills basic requirements in terms of code quality, handling of sensitive data, and interaction with the mobile environment. A testing process must be in place to verify the security controls. This level is appropriate for all mobile applications.
- MASVS-L2: Defense-in-Depth
- MASVS-L2 introduces advanced security controls that go beyond the standard requirements. To fulfill MASVS-L2, a threat model must exist, and security must be an integral part of the app’s architecture and design. Based on the threat model, the right MASVS-L2 controls should have been selected and implemented successfully. This level is appropriate for apps that handle highly sensitive data, such as mobile banking apps.
- MASVS-R: Resiliency Against Reverse Engineering and Tampering
- The app has state-of-the-art security, and is also resilient against specific, clearly defined client-side attacks, such as tampering, modding, or reverse engineering to extract sensitive code or data. Such an app either leverages hardware security features or sufficiently strong and verifiable software protection techniques. MASVS-R is applicable to apps that handle highly sensitive data and may serve as a means of protecting intellectual property.
Examples of Security Level Usage:
MASVS-L1:
- Fitness apps, Transport apps that handle various types of sensitive data, such as user profiles, health records, location, preferences, and contacts which exposed the login user. Incase required advance protection such as Biometric authentication, SSL Pinning, Certificate Transparency for high-value transactions, they should be applied MASVS-L2/ MASVS-L2 + R.
MASVS-L2:
- Banking: Apps that allow users to access their accounts, transfer money, pay bills, and manage their investments. The app handles sensitive data such as personal and financial information and performs high-value transactions.
MASVS-L1+R:
- A gaming app that allows users to play online games with other players, chat with them, and buy virtual items. The app may/may not handle any sensitive data or perform any high-value transactions, but it has valuable intellectual property and business logic that could be stolen or copied by competitors or malicious users. The app operates in a hostile environment where reverse engineering and tampering are likely or have a high impact.
MASVS-L2+R:
- Financial Industry: Online banking apps that allow the user to move funds, where techniques such as code injection and instrumentation on compromised devices pose a risk. In this case, controls from MASVS-R can be used to impede tampering, raising the bar for malware authors.
CONCLUSION
By applying OWASP MASVS, we can prevent almost of security issues for mobile application. However, the effort is spent for it is not small and we also need more effort for security testing. Let categorize how much sensitive of your application and your budget, then pick up suitable level of security.
This blog is not providing you very details of how to implement it in mobile applications, but we can understand how important is it and also introduce a standard for Security in Mobile Applications.


