Welcome to “ZAP 101: Security Testing Introduction”! In this blog, we will provide you with a beginner-friendly introduction to using ZAP for security testing, even if you don’t have prior experience in this area. We understand that security testing might sound intimidating, so we’ve made sure to include essential concepts and terminology to ease you into the topic.
What is ZAP?
The Zed Attack Proxy (ZAP) is an open-source web application security testing tool developed by the Open Web Application Security Project (OWASP). What sets ZAP apart is its versatility, catering to users with varying skill levels in the realm of security testing. From developers to security testing specialists, ZAP offers functionality for everyone.
1. Accessibility Across Multiple Operating Systems
ZAP’s developers have gone the extra mile to ensure accessibility by providing versions for each major operating system, including Windows, macOS, and Linux. Moreover, Docker support means users are not tied to a specific OS, giving them the flexibility to run ZAP seamlessly on various platforms.
2. Suitable for Novice Testers
For those new to security testing, ZAP serves as a gentle yet effective introduction. The user-friendly interface guides testers through the testing process and helps them identify vulnerabilities with ease. Its automated scanning capabilities enable beginners to detect common security issues without the need for in-depth knowledge of security testing.
3. Comprehensive Features for Advanced Users
On the other end of the spectrum, ZAP offers a wealth of advanced features that cater to seasoned security testing specialists. By acting as an intercepting proxy, ZAP captures and analyzes HTTP/HTTPS requests, allowing testers to delve deep into the application’s traffic. This feature is particularly valuable for in-depth manual testing and the simulation of sophisticated attack scenarios.
ZAP’s Role in Security Testing
Security testing plays a vital role in the software development life cycle, and ZAP is specifically designed for web application security testing. Here’s how ZAP contributes to ensuring the security of web applications:
- Vulnerability Scanning: ZAP conducts automated scans of web applications to identify common security vulnerabilities, such as Cross-Site Scripting (XSS), SQL injection, Cross-Site Request Forgery (CSRF), and more. These automated scans significantly reduce the time and effort required to detect potential issues.
- Penetration Testing: ZAP allows security testers and ethical hackers to perform manual penetration testing. They can use ZAP’s interactive features to simulate real-world attack scenarios, gaining a deeper understanding of the application’s security posture.
- Intercepting Proxy: ZAP acts as an intercepting proxy, sitting between the client and the server. It captures and analyzes HTTP/HTTPS requests and responses, giving testers the ability to inspect and modify the application’s traffic. This enables the identification of security flaws that might otherwise remain unnoticed.
- Reporting and Documentation: After conducting security tests, ZAP generates detailed reports containing identified vulnerabilities and potential exploits. These reports help developers and security professionals understand the issues better and take appropriate measures to fix them.
Getting Started with ZAP
To begin using ZAP, follow these steps:
Download and Install
ZAP is freely available for download on the OWASP website. Install it on your preferred operating system.
- you must install Java 11+ separately for Windows, Linux, and Cross-Platform versions.
- After the installation process is finished, simply launch ZAP, and you’ll be prompted to read and accept the license terms.
- Upon reviewing the terms, click on the “Agree” button to proceed with the installation.
- Once the installation is complete, ZAP will automatically start and be ready for use.
After Installing the ZAP, you will face the below popup.
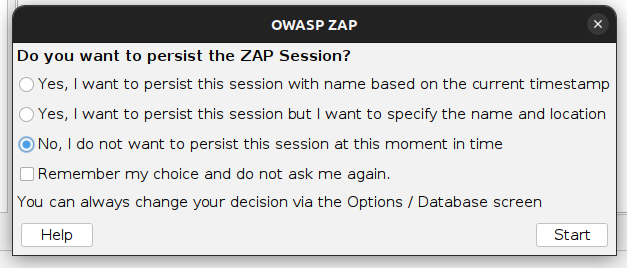
At this moment, choose the “No” option to avoid persisting in the current session, and then click on the “Start” button. By doing so, the ZAP sessions will not be saved and will remain non-persistent for the time being.
ZAP Desktop UI is thoughtfully designed
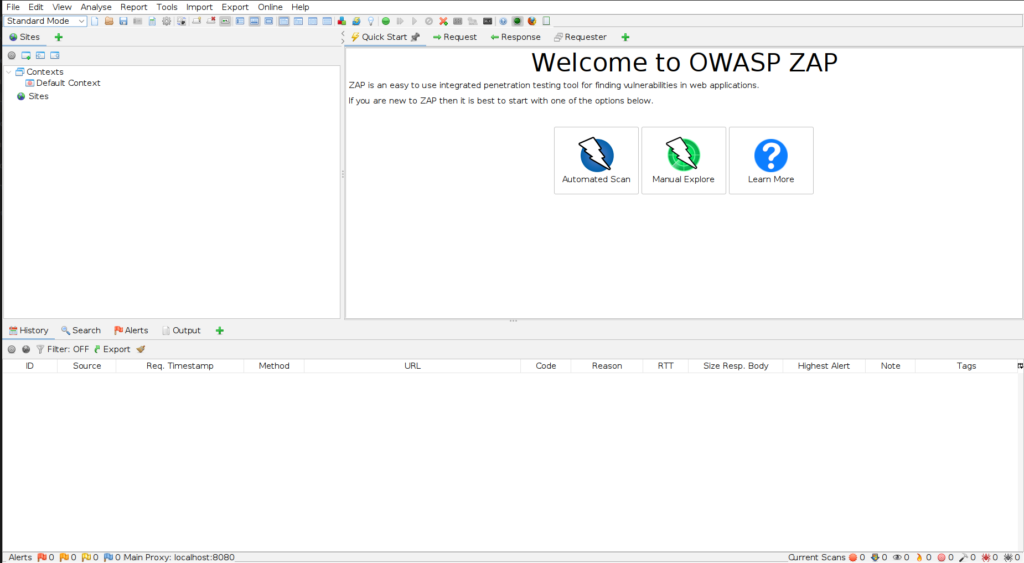
- Menu Bar: This essential component grants access to various automated and manual tools. Users can navigate various functionalities and features from the easily accessible menu options.
- Toolbar: Located at the top, the Toolbar houses buttons that provide quick and convenient access to the most frequently used features. This streamlines the user’s workflow and enhances efficiency during security testing.
- Tree Window: The Tree Window serves as a central hub, displaying both the Sites tree and the Scripts tree. Here, users can effortlessly manage and organize their testing targets and scripts.
- Workspace Window: The Workspace Window takes centre stage, showcasing requests, responses, and scripts. Users can edit these elements as needed, facilitating a comprehensive and customized testing process.
- Information Window: An indispensable part of the UI, the Information Window presents detailed information regarding the automated and manual tools at the user’s disposal. This valuable insight empowers testers to make informed decisions during their testing endeavours.
- Footer: Located at the bottom, the Footer provides a concise summary of the discovered alerts and the current status of the primary automated tools. This real-time feedback keeps users updated and informed about potential security issues.
Initiating an automated scan with ZAP
Running a Quick Start Automated Scan with ZAP is a straightforward and efficient process, allowing users to quickly identify potential security vulnerabilities in their web applications.
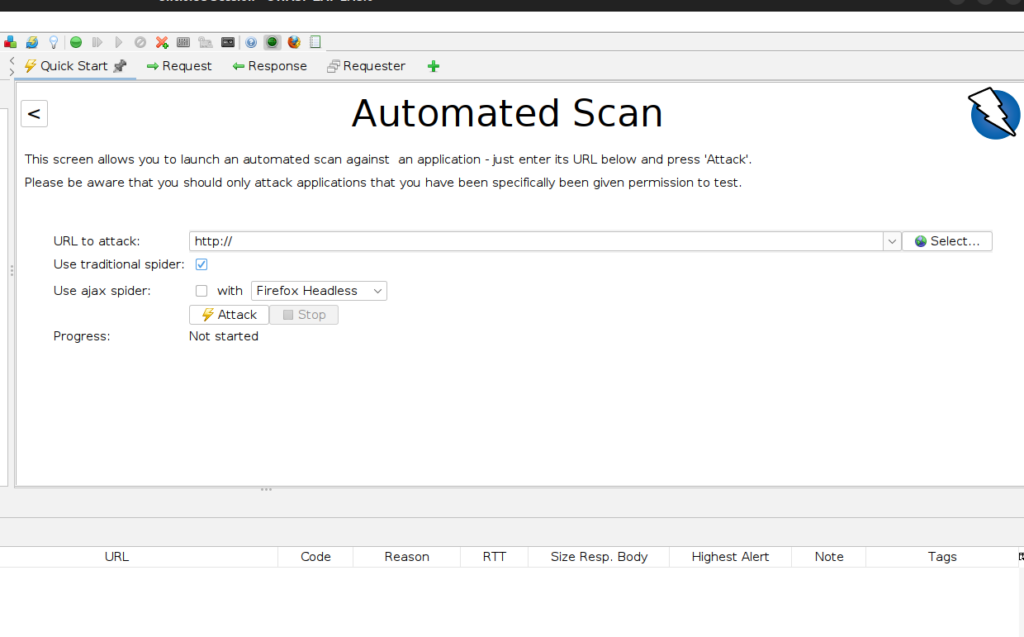
- Open the ZAP application and ensure it’s properly configured as an intercepting proxy between your browser and the target web application.
- Navigate to the web application you want to test using your preferred web browser.
- click on the “Quick Start” button.
- Click the Attack.
ZAP switches to the active scanner mode, where it becomes more assertive. It launches attacks on all the pages, functionalities, and parameters it discovered during the crawling phase. By actively probing for vulnerabilities, ZAP ensures a comprehensive evaluation of the web application’s security, identifying potential weaknesses that might not be evident during passive scanning.
- Passive Scanning: Currently, ZAP has been conducting passive scans of your web application by observing all requests and responses passed through its proxy. Passive scanning is entirely non-intrusive and does not modify any responses, making it a safe and risk-free process.
- Active Scanning: In contrast to passive scanning, active scanning involves real attacks using known techniques against the selected targets. The goal of active scanning is to uncover additional vulnerabilities that might not be evident during passive scanning.
By leveraging both passive and active scanning techniques, ZAP provides a comprehensive and thorough security assessment of your web application. Passive scanning gives a broad overview and helps in identifying potential vulnerabilities, while active scanning delves deeper to uncover more complex security issues. Always prioritize ethical practices and ensure proper authorization before conducting any active scans on web applications.
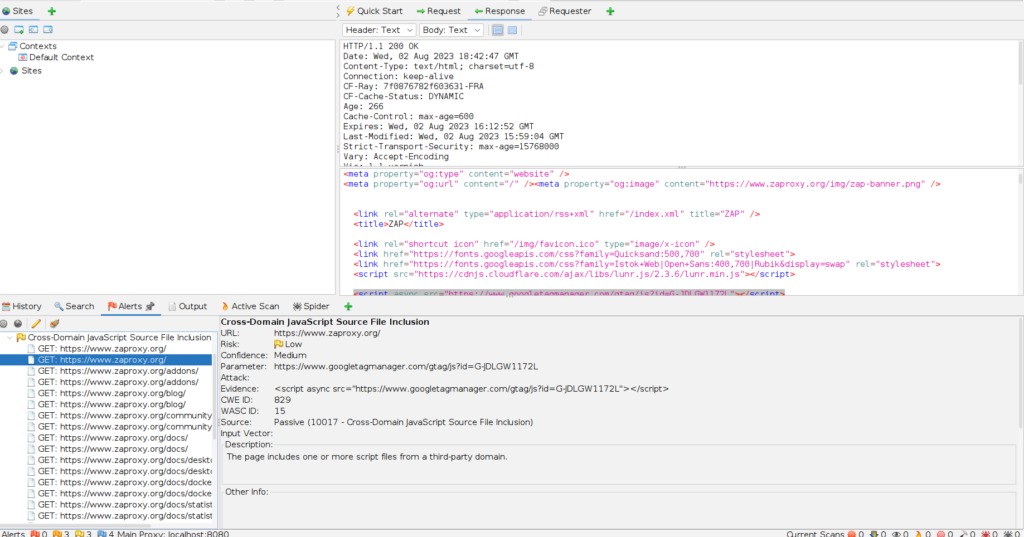
View Alerts and Alert Details
Located on the left-hand side of the Footer, you’ll find a comprehensive count of the Alerts discovered during your testing. These Alerts are intelligently categorized based on their risk levels. The risk categories include:
To access the alerts generated during your test, follow these steps:
- Click on the “Alerts” tab located within the Information Window.
- In the same Information Window, you will find a list of alerts displayed. Click on each alert to reveal detailed information, such as the URL and the specific vulnerability detected. This information will be showcased on the right side of the Information Window.
- For further analysis, head over to the Workspace Window and click on the “Response” tab. Here, you can view the contents of the header and body of the response. The part of the response that triggered the alert will be conveniently highlighted, allowing you to pinpoint the exact source of the vulnerability.
